There are many file transfer protocols out there, out of which AS2 (Applicability Statement 2) and SFTP (Secure File Transfer Protocol) are pretty popular. Both these protocols are used for secure file sharing between users.
Organizations often feel perplexed about which one is better for their business-critical file transfers. In this post, we are going to dive into the differences between AS2 and SFTP. Which one to use? What are the features and functionalities of both protocols? And what makes one different from the other?
What is AS2?
Before we get into AS2, we first need to understand AS1. AS1 stands for Applicability Statement 1, a file transfer protocol launched in the 1990s by a business communications company EDIINT.
We know that EDI (Electronic Data Interchange) is a format large organizations use to exchange their digital information related to invoices, purchases, etc., with other enterprises. EDIINT is an acronym for EDI over INTernet. Back in the day, large business organizations that commonly used EDI for electronic transactions were seeking a means to exchange EDI-formatted data streams securely via the public internet. By the end of the 1990s, EDIINT established AS1- a file transfer protocol that can securely execute digital transmission over the public internet. It was a standardized technology, as recognized by various web standards entities.
The AS1 protocol used SMTP (Simple Main Transport Protocol) – a standard for exchanging communications. But AS1 was not widely adopted by the large IT organizations due to their uncertainty of switching from VAN networks to transfers over the public internet using AS1. Another reason for not using AS1 was the IT department’s fear that EDI traffic may overload corporate SMTP email servers, as AS1 is highly on secure SMTP packets. Furthermore, SMTP emails were not robust enough with innovative features to ensure on-time delivery of SMTP emails.
These instigated EDIINT to launch the new AS2 protocol in 2001 based upon HTTP protocol instead of SMTP. AS2 uses a secure HTTPS connection and enacts encryption of messages, referred to as AS2 messages. Hence, it allows real-time and direct communications for the transfer of EDI data between enterprises. The popularity of the internet and leveraging of HTTP together resulted in wide adoption and implementation of the AS2 protocol.
Unlike AS1, AS2 messages are compressed and signed; only then they’re transmitted over HTTPs through a secure SSL tunnel. Moreover, AS2 also allows you to request a receipt (Message Disposition Notification), which will alert the sender as soon as the recipient decrypts the received message. This process is often referred to as non-repudiation. The recipient will create, sign and return the receipt (also known as NRR – Non-repudiation of Receipt) to the sender after decrypting the message to legally confirm that the AS2 Messages were delivered without any tampering in transit. Even today, AS2 protocol remains a popular standard used by most retailers in E-stores and brick and mortar.
In summary, AS2 employs two methods of security to protect sensitive data in transit, viz. Industry-level encryption standards and digital certification.
What is SFTP?
Secure File Transfer Protocol (SFTP), also known as SSH File Transfer Protocol, is a file transfer protocol that uses a secure tunneling protocol viz. Secure Shell 2 (SSH2). SSH2 emulates an FTP connection to create an encrypted channel for your file transfers using TCP port 22.
SFTP is firewall-friendly, as it requires only one port. It is one of the most uncomplicated protocols used for encrypted file transfer. Data transmitted between an SFTP server and client is secured via encryption compute and the use of public/private keys. All of these together offer robust protection known as public-key authentication. Or, users can also authenticate transmissions with an SSH key or a password.
The security layer of SFTP was developed by IETF (Internet Engineering Task Force). It encrypts the data-in-transit to protect it as it moves across the internet and then decrypts it as it reaches its final destination. One downside is that SFTP does not offer non-repudiation or message management like AS2 protocol. And interoperability is one of the main issues with SFTP.
SFTP is an excellent alternative to less secure manual scripts or FTP tools. In addition, it provides a higher level of security to organizations wanting to transfer files with their trading partners, employees, vendors, etc.
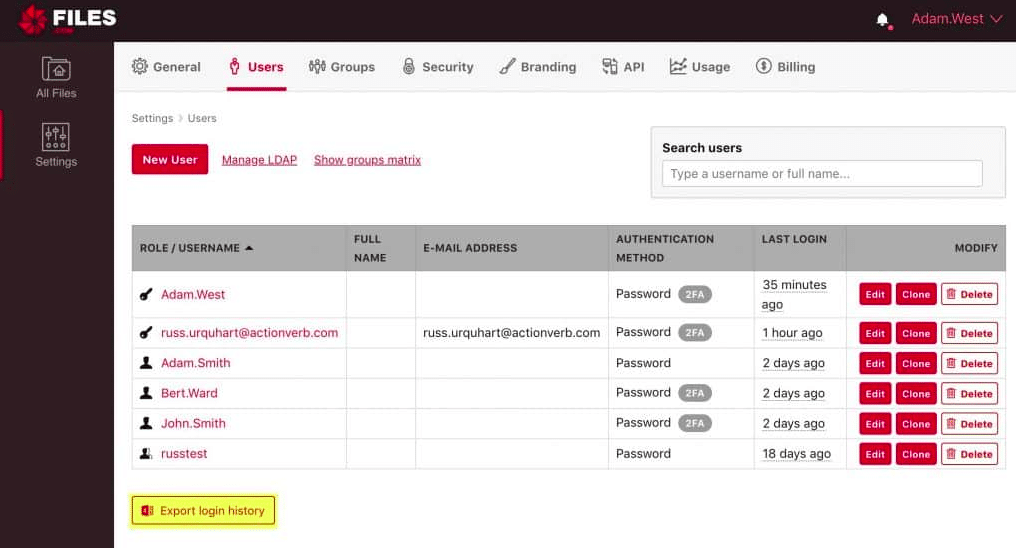
Popular platforms like SolarWinds and Files.com support SFTP protocol to help you with secure file transfers as well.
Main Differences between AS2 and SFTP protocols
1. Encryption
Every IP communications protocol is built differently with different features. In addition, each of them may have a different approach to secure data transmission. For example, some protocols only focus on encrypting transport channels, whereas others secure the actual data, also known as payload encryption.
- SFTP does not offer security and authentication itself. Instead, it relies upon the underneath protocol for security. To establish a secure connection, you may need to leverage Virtual Private Network (VPN) or use SFTP as a subsystem to the SSH protocol. Such a combination of protocols will encrypt the entire transport channel to secure the data. In short, the transport is protected, not the payload itself. This is what influences SFTP’s cost and interoperability.
- AS2 protocol focuses on payload encryption itself rather than the transport channel, thereby offering robust end-to-end security. As an option, you can even encrypt the transport channel with SSL along with payload encryption. Apart from this, AS2 can run a hashing process, ensuring the files aren’t tampered with as it moves.
2. Non-repudiation
Non-repudiation is another security token that confirms that a trusted, claimed sender sends a packet.
- SFTP does not address non-repudiation.
- AS2 makes use of digital certificates to make sure the packets are delivered to the authentic recipient only. These certificates will secure the messages in transit and also verify the sender. Know that the user needs to manage the digital certificates that your company and trading partners use. Such management commonly includes generating and tracking certificates and processing canceled or expired certificates.
3. Message Management
When it comes to B2B, organizations seek a standard means to ensure that their messages reach their intended destination and are successfully decrypted.
- SFTP does not entirely address message management. For example, SFTP will send a confirmation notification of the bytes transmitted once the document file is sent. But, it does not indicate whether the message was successfully processed or not.
- AS2, on the other hand, notifies a status message known as the “Message Disposition Notification” (MDN). AS2 protocol will place the message in an envelope and transfer it over the internet. This way, you will know that the message was successfully extracted from the envelope and processed. Once the message is sent, AS2 protocol will send an MDN to notify whether the document was successfully removed from the envelope or not.
4. Interoperability and Ease of Use
IT organizations would want to choose a protocol that seamlessly creates a connection with the trading partners.
- Most commonly, organizations use VPNs as a technology to secure their internet-based communications within the organization. But, using SFTP over a VPN to establish communication between two different organizations may lead to interoperability problems. Your trading partners may likely be using a VPN technology from a third-party vendor. For a robust connection, you need to ensure that your VPN software is compatible and aptly configured to work with their VPN. The good thing is that SFTP software requires minimal configuration. However, intermingling SFTP and FTPS software from different vendors may give rise to interoperability issues.
- AS2 standard is meticulously developed for seamless B2B transactions over the public internet. AS2 protocol was widely adopted and implemented by large IT organizations as it offers inbuilt business-grade transaction management. Furthermore, Drummond Group supports AS2 standards and performs certification testing on software from third-party vendors to check its interoperability with products from other vendors. In other words, if you buy any two products listed under the Drummond-certified products, they are guaranteed to work together seamlessly without any interoperability challenges.
5. Cost
- The most significant advantage of SFTP is that it is cost-effective. It is a reliable and secure file transfer protocol. Plus, it does not require much configuration. Users can easily set up the connection as long as they know the intended server name to be reached. However, adding security, message management, and other B2B features to SFTP increases the overhead cost.
- AS2 standard requires unique software, certificate administration, and technical expertise, thus resulting in high overhead. Users can cut down some of these costs by working with a service provider. And to reduce operating costs, you can offload management operations instead of running an AS2 solution by yourself.
What is an AS2 Server?
AS2 Server is an application element that helps file transfers or electronic business documents with business partners via AS2 protocol. The AS2 Server commonly contains two functionalities viz. They are sending EDI documents/AS2 messages and receiving them. Apart from this, AS2 Servers need to support other features such as data-in-transit encryption, HTTP/HTTPS, digital certificates, digital signatures, and message management. AS2 Servers that are Drummond-Certified undergo a robust testing process to offer interoperability and reliability with other certified AS2 solutions.
Which protocol is best for organizations?
To conclude, IT organizations may have myriads of choices regarding secure communication protocols for EDI documents. Out of AS2 and SFTP protocols, the AS2 standard best addresses essential file transmission needs technical expertise, and certificate administration. Nevertheless, due to its full-blown features, most large-scale retailers leverage AS2 to transmit EDI documents.
When to choose SFTP?
If you want to opt for SFTP for its simplicity, consider a reliable provider such as SolarWinds or Files.com to fill up the gaps in its functionality.
SFTP is extremely popular amongst IT organizations due to its firewall-friendly nature and strong authentication abilities. For encryption, SFTP supports Triple DES, AES, and algorithms like Blowfish. And for authentication, organizations wanting to use SFTP may test the connection using an SSH key, user ID and password, or both. Many SFTP solutions like SolarWinds and Files.com support two-factor authentication to provide top-notch security.
Files.com offer access to a 7-day free trial.
The rest of the business industry (other than retailers) prefers SFTP over AS2 protocol. Select SFTP if you want to leverage higher levels of authentication and firewall options. SFTP employs user ID/password or SSH keys or a combination of both to authenticate a connection between servers.
Moreover, SFTP is extremely easy to implement. It is a firewall-friendly protocol; hence, it requires only one port (commonly port 22) to initialize authentication requests, assign commands, and transfer information from organizational systems to other servers.
When to choose AS2 protocol?
Back in 2002, Walmart leveraged AS2 protocol as a standard for their EDI transactions, and other third-party vendors, retailers, and suppliers had to comply as well.
In other words, select AS2 protocol:
- If you work in the retail industry and your business partner requires you to use the AS2 protocol, it will be your ultimate solution.
- Secondly, if you’re looking for an easy way to meet regulatory compliance standards and meet your trading partner’s requirements.
- If you would like to have synchronous or asynchronous MDN receipts to ensure that the intended recipient has received and successfully decrypted the AS2 messages.
Apart from this, the AS2 protocol also offers the following benefits:
- Ability to retrieve or send files of any size
- End-to-end file encryption to secure sensitive information and files
- Non-repudiation that validates file integrity and confirms successful file transfer
- Uses secure technologies such as SSL Certificates, HTTPS, file hashing and S/MIME
- Authentication of the sender as well as recipient to ensure their reliability
- MDNs to verify successful decryption
Lastly, solutions that use AS2 can attain Drummond Group Certification as legal proof of their compliance to the AS2 standard. This third-party certification validates that the certified AS2 answer is one of the best compliant solutions.
AS2 Protocol FAQs
What is AS2 protocol?
AS2 (Applicability Statement 2) is a secure and reliable protocol used for exchanging business-to-business (B2B) data over the internet. It is a widely adopted standard for electronic data interchange (EDI) and is used by organizations to exchange business documents such as purchase orders, invoices, and shipping notices.
How does AS2 protocol work?
AS2 protocol works by using digital certificates and encryption to securely transmit data over the internet. It uses HTTP or HTTPS as the underlying transport protocol, and the data is usually sent using MIME (Multipurpose Internet Mail Extensions) format. The protocol also includes acknowledgments and receipts to ensure that data is received and processed successfully.
What are some benefits of using AS2 protocol?
Some benefits of using AS2 protocol include improved data security and reliability, faster and more efficient document exchange, reduced costs associated with paper-based transactions, and enhanced supply chain visibility and collaboration.
What is the difference between AS2 protocol and SFTP?
AS2 protocol and SFTP (Secure File Transfer Protocol) are both used for secure file transfer, but they differ in how they transmit data and the types of applications they are best suited for. AS2 is typically used for exchanging structured data between business partners, while SFTP is used for more general file transfers.
How does data transmission differ between AS2 and SFTP?
AS2 uses HTTP or HTTPS as the underlying transport protocol and is designed to send structured data, such as EDI documents, in a secure and reliable way. SFTP, on the other hand, uses SSH (Secure Shell) for secure file transfer and can be used for any type of file transfer.