As an organization’s footprint expands, the risk of digital breaches increases as well. Research suggests that 30% of breaches take place due to vulnerabilities or shadow IT assets within the cloud that the IT security team fails to identify. Here’s our list of the best Attack Surface Monitoring Tools: Aikido – EDITOR’S CHOICE An end-to-end […]
The Best Attack Surface Monitoring Tools
The Best Server Patch Management Tools
Software patch management is a process in which a piece of code is tailored to fix a problem, error, or bug in the application. This helps a network of computers to perform to the best of their ability and keep them up-to-date. The server patch management process is extensive. Right from detecting any missing patches […]
The Best Splunk Alternatives
We all know that Splunk is one of the most famous log management tools on the market, but it isn’t for everyone. Several more Splunk alternatives are a better fit for enterprises that need to monitor a massive volume of data. In this article, we’ll look at the best Splunk alternatives available. There are tools […]
Export AD Group Members with PowerShell
Maybe you are trying to find a list of users that belong to the Administrator’s group, or you probably want to know who has access to which folder. Anyone from IT managers, security auditors, or even third-party services might want to get a list of Active Directory group members for several reasons. Unfortunately, the built-in […]
The Best Python Monitoring Tools
There are many programming languages, and Python ranks among one of the most popular choices today because of its simplified syntax. There is a lot of emphasis on the natural language and this is why python codes are written and understood more easily when compared to codes written in other programming languages. The popularity of […]
The Best Disk Imaging Software
Are you backing up what’s most important to you? Between ransomware, sudden drive failures, and accidental deletion, there are plenty of ways data can get lost or destroyed. In this article, we’ll dive into some of the best disk imaging software solutions, and review how each one can make creating backups a simple and reliable […]
The Best Vulnerability Assessment and Penetration Testing (VAPT) Tools
Staying on top of your system’s vulnerabilities is the key to network security. But that’s not easy given the huge complexity and the many failure points present in it. This is where Vulnerability Assessment and Penetration Tools (VAPT) come in handy as they do the penetration testing and generate reports that contain a list of […]
The Best DDoS Protection Services
A DDoS attack is carried out with the help of several infected computers asking to access your network’s internet resources at the same time. This leads to a slowdown in your websites and applications. It may not only cause financial loss but it can also lead to a dip in customer loyalty. Robust DDoS software […]
The Best Penetration Testing Tools
Penetration testing tools are applications used to detect network security threats. Penetration testing, also referred to as “pen test”, is an authorized simulated attack on your system attempted by security experts (white-hat hackers) to evaluate your computer systems’ security. These attacks simulate the real-world attacks carried out by black-hat hackers (criminal hackers). The tests will […]
The Best RMM Software & Tools
Remote Monitoring and Management Software is an application tool used by Managed IT service providers to remotely and ardently monitor the endpoints, computers, and other client assets on their networks. These tools offer in-depth visibility into connected endpoints, they monitor various actions taken and keep tabs on the overall performance of the network. Here is […]
The Best Remote Desktop Connection Managers
Remote Desktop Connection Managers are very handy pieces of software. They give you a single point from where you can access your saved remote connections. This means that you don’t have to keep a disparate list of your servers somewhere else. If you need to connect remotely to multiple machines, then this is the kind […]
The Best SSH Clients for Windows – Save Connections, Multi-Tabbing & More!
Here’s our List of the Best SSH Clients for Windows – Save Connections, Multi-Tabbing & More! Get your FREE DOWNLOAD Today & Get Started with SSH Now!
WSUS Tools & Software for Maintaining Windows Updates
Here’s the Best Picks of Best WSUS Tools & Software for Maintaining Windows Updates & more in Your Network to Ensure Updates are Always on Time!
The Best Network Monitoring Software & Tools – A Thorough List & Breakdown of Each!
We Review 20 of the Best Network Monitoring Software & Tools for Your Network and Infrastructure! We Dive Deep into Each Software, Price and Feature Sets!
The Best Systems Management Tools
Here’s our List of the Best Systems Management Software & Tools for an All Encompassing Management Solution
The Best Patch Management Tools
Here’s A Full List of the Top 11 Patch Management Tools and Software for Keeping your Windows, Linux & Other Critical Systems Up-to-Date at All Times!
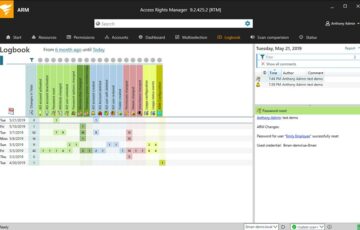
SolarWinds Access Rights Manager – Here’s a Review of this Great Active Directory Auditing Tool!
Access Rights manager from Solarwinds is One Great Tool! Making Auditing Active Directory Users, Files and Shraes for Permissions have never Been easier – Here’s a Quick look into the Software!
The Best System & Event Log Monitoring
Finding the Best Log Manager Software & Tools for your Infrastructure is a Daunting Task – So here’s a List of the Top Tools & Software
Dameware Review – Remote Computer Management, Control & Administration Software!
Dameware is a Great Remote Administration and Management Tool that Deserves More credit than most Admins give it – We’ve Reviewed it as Thoroughly as possible with Screenshots and System Requirements!
Best Wake-on-LAN Software & Tools for WoL for your Servers/PC
Here’s a List of the Best Wake On Lan Tools & Software for assisting in sending Magic Packets & WOL Commands remotely to Any PC, Server, laptop, etc
Progress WhatsUp Gold Review and How-To Setup Guide
We’ve gone through an extensive Review of IPSwitch’s WhatsUp Gold 2017 for network Monitoring along with a Full How-To setup Guide.
SolarWinds Network Performance Monitor (NPM) Review & How-To Setup Guide
Solarwinds Network Performance Monitor is by Far one of the Best (if not the Best) network Monitoring Solutions on the market – We go through the Process of Installing, Configuring and setting it up!
SolarWinds NPM vs Nagios for Bandwidth & Network Monitoring and Management
We breakdown the differences between Solarwinds and Nagios for Network and Infrastructure Monitoring
PRTG vs MRTG Comparison & Differences for Network Monitoring/Management
Here’s a quick breakdown of the Differences between PRTG vs MRTG for Network and Computer Management & Monitoring Tasks.
The Best WiFi Analyzers and Scanners for WINDOWS for Strength, Channel & Spectrum Analysis
Monitoring and Analyzing Wifi in your Network will not only track down high-bandwidth users, but will help you diagnose Dead spots and weak signal issues that arise from buildings, walls and other electronics.
PRTG Network Monitor Review, HowTo Setup & Monitor Cisco Devices & Windows Servers
PRTG is by far one of the Best Network Monitoring tools on the market – We’ve put together an extensive Review of PRTG Network Monitor along with a HOWTO Guide for setting it up and Configuring it.
Sysmalogics Active Directory Report Builder Review and Overview
We review Sysmalogics Active Directory Report Builder for building Reports from AD – It’s highly customizable and fully featured report builder that gives other software manufacturers a run for their Money!
The Best Event Log Analysis Tools & Software for Windows/Open Source (FREE & PAID)
Keeping Track of CRITICAL Events and analyzing your Event logs is extremely Important – Much of what happens to your everyday servers and infrastructure can tracked and detected through your Logs and having a Log Analyzer will help you in that process.
The Best Spiceworks Alternatives, Competitors & Replacements
Spiceworks is great for starting out when your looking to keep an eye on your Network and catalog Software and Hardware – But when its time to implement a more Robust Monitoring solution, it doesn’t Cut it.
The Best Open Source Network Monitoring Tools and Software (Linux/Windows)
We’ve compiled a list of the top open-source network monitoring solutions, software and tools for keeping an eye on your network. These are FREE and have great functionality for Network Management!