Finding the Best Log Manager software and tools for your network and infrastructure shouldn't be a guessing game – We've compiled a list of the top Logging tools & software and rated them by features, price and capabilities.
Keeping track of your system logs is not an easy thing to do, even at the best of times.
Here is our list of the top log management tools:
- ManageEngine OpManager – EDITOR’S CHOICE Excels in comprehensive event log monitoring, offering real-time insights and robust security features. It integrates seamlessly with network and application management systems, making it a versatile and powerful tool for maintaining network health and security. Download a 30-day free trial.
- Site24x7 Log Management – FREE TRIAL A log server, consolidator, and processor that is available from several plans offered by a cloud-based system monitoring platform.
- ManageEngine EventLog Analyzer – FREE TRIAL A log management and SIEM (security) tool that is available in free and paid versions. Available for Windows Server and Linux.
- Paessler PRTG – FREE TRIAL A package of network, server, and application monitors that includes a Windows Event Log Sensor and a Syslog Receiver Sensor. Installs on Windows Server.
- Datadog Log Management A log server and manager, called Ingest, and a log archiving system, called Retain or Rehydrate.
- Lepide Collects, stores, and manages Windows Events and WC3 log messages and includes compliance auditing tools. Installs on Windows Server.
- McAfee Enterprise Log Manager A log server, consolidator, and manager that is part of the McAfee Enterprise Security Manager and contributes towards data security standards compliance reporting and auditing. Installs on a bare metal server as a virtual appliance.
- SolarWinds Security Event Manager A full system security too that can be used in part to manage log messages and files. This system includes log analysis functions for system management as well as intrusion detection. Runs on Window Server.
- Corner Bowl Server Manager A server, consolidator, and manager for Syslog, Event Log, and Azure AD logs that is also a log analyzer with HIPAA and PCI-DSS reporting capabilities. Runs on Windows and Windows Server.
- Splunk A well-known free log manager that has paid extensions for functions such as security analysis. Available for Windows, Windows Server, macOS, Linux, and Unix.
Most people don’t even consider log storage as something that needs to be taken into consideration at all.
But when it comes to keeping your systems compliant with auditing procedures and advanced troubleshooting, it is a must have solution for any business.
Once logs are stored properly, they can then be searched with specialized software that can help to pinpoint system issues and even clues about security problems on your network.
We have rounded up some of the Best Log Management Solutions that are available today so that we can help you decide which solution is best for you and your company.
Our methodology for selecting the best log manager & monitoring tool:
We've broken down our analysis for you based on these key criteria:
- Capability to generate comprehensive compliance reports.
- Real-time monitoring and event correlation abilities.
- Features for advanced search and forensic analysis.
- Effectiveness in incident response and automated remediation.
- Ease of integration with existing IT infrastructure.
The Best Log Manager & Monitoring Tools:
1. ManageEngine OpManager – FREE TRIAL
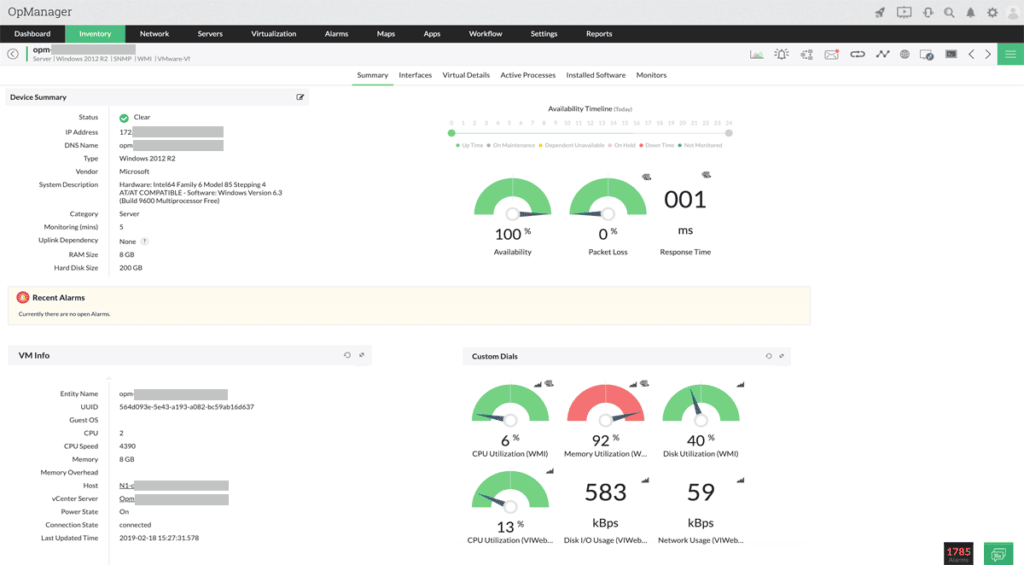
ManageEngine OpManager is one of the best log management software solutions available, providing robust event log monitoring capabilities to track and analyze logs generated by network devices. By offering real-time insights into network performance, OpManager helps detect network issues before they impact operations. It excels in monitoring Windows event logs, including application, system, and security logs, allowing IT teams to diagnose application and operating system failures efficiently.
Key Features:
- Comprehensive Network Monitoring: Real-time monitoring for a wide range of network devices, servers, and applications.
- Advanced Traffic Analysis: Utilizes technologies like NetFlow, IP SLA, and CBQoS for detailed traffic analysis and bandwidth management.
- Automated Alerts: Sends threshold-based alerts via SMS and email to enable immediate action on potential issues.
- Configuration Management: Automates network configuration tasks, ensuring compliance with industry standards and easy management of changes.
- Customizable Dashboards: Offers intuitive and customizable dashboards for real-time visibility and control over the network.
- Integrated ITSM Tools: Seamlessly integrates with IT service management tools for efficient troubleshooting and problem resolution.
The software also enhances network security by monitoring critical security logs, such as failed logons and account lockouts, thereby protecting the network from internal threats. OpManager's integrated approach to event log monitoring eliminates the need for additional consoles, making it part of a comprehensive network, server, and application management solution. This integration streamlines operations and ensures that IT teams can manage logs alongside other network management tasks from a single interface.
With customizable rules and out-of-the-box support for mission-critical applications like Exchange, IIS, and SQL servers, OpManager is a versatile and powerful tool for maintaining network health and security.
Why do we recommend it?
ManageEngine OpManager is recommended for its robust feature set, including real-time monitoring, automated alerts, and comprehensive traffic analysis. These capabilities help ensure optimal network performance and reliability, making it a powerful tool for any IT team.
Who is it recommended for?
OpManager is ideal for medium to large enterprises and managed service providers (MSPs) looking to efficiently monitor and manage diverse network environments. Its scalability and customizable features make it suitable for complex network infrastructures.
Pros:
- Comprehensive Device Support: Supports a wide range of network devices and technologies, ensuring thorough network oversight.
- Real-Time Monitoring: Provides real-time monitoring and alerts, allowing for quick response to potential issues.
- User-Friendly Interface: Features an intuitive and customizable interface, making it easy for IT teams to manage and monitor their networks.
- Automated Configuration Management: Reduces manual workload by automating configuration tasks and ensuring compliance with industry standards.
- Seamless Integration: Integrates smoothly with various ITSM tools, enhancing troubleshooting and issue resolution.
Cons:
- Complex Initial Setup: Initial configuration can be time-consuming and complex, requiring significant effort to fully integrate into existing systems.
You can start by downloading the 30-day free trial.
EDITOR'S CHOICE
ManageEngine OpManager is our top choice for log management due to its comprehensive event log monitoring capabilities that provide real-time insights into network performance. Its robust functionality includes monitoring Windows event logs, such as application, system, and security logs, which are crucial for diagnosing application and operating system failures. OpManager excels in enhancing network security by detecting critical security events like failed logons, account lockouts, and unauthorized access attempts.
This proactive approach helps protect the network from internal threats and ensures the integrity of the IT infrastructure. Additionally, OpManager's integrated event log monitoring eliminates the need for additional consoles, allowing IT teams to manage logs alongside other network management tasks from a single interface.
With customizable rules and out-of-the-box support for monitoring essential applications like Exchange, IIS, and SQL servers, OpManager simplifies and strengthens the overall network management process, making it an indispensable tool for maintaining network health and security.
Download: Get a 30-day FREE Trial
Official Site: https://www.manageengine.com/network-monitoring/eventlog-monitoring.html
OS: Windows, Linux, Cloud-based
2. Site24x7 Log Management – FREE TRIAL
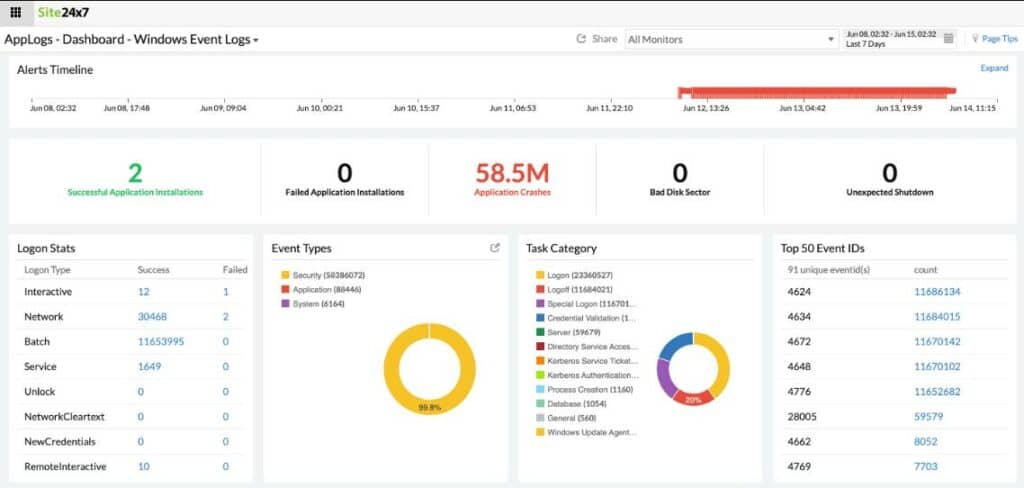
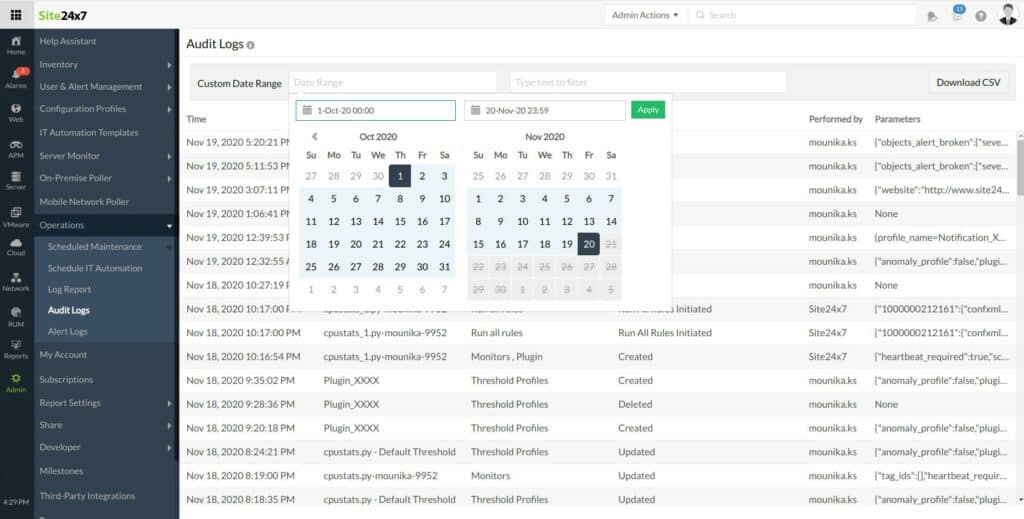
Site24x7 is a SaaS infrastructure monitoring platform, based in the cloud. The services of this platform are offered on subscriptions with divided between several packages. Each page can be accessed as a standalone tool and there is also a combined package, called the All-in-one plan.
Key Features:
- Cloud-Based Monitoring
- AI-Enhanced Root Cause Analysis
- Multi-Cloud SQL Monitoring
- Application Stack Dependency Views
Why do we recommend it?
Site24x7 offers an effective cloud-based solution with AI-enhanced root cause analysis, making it a powerful tool for fast and efficient technical issue resolution.
The Log Management system of Site24x7 is not available as an independent service. Instead, it is bundled in with the subscription plans. These are:
- Website Monitoring
- Infrastructure
- Application Performance Monitor
- All-in-one
- MSP
In most cases, a standard subscription gets a processing allowance of 500 MB of log data per month. Exceptions to this rule are the Elite and Enterprise editions of the All-in-one plan on the MSP plan, all of which get a data processing level of 1 GB per month included. Subscribers are offered a monthly capacity upgrade for log data processing.
The Log Manager collects and stores log messages from Windows Events, Syslog, applications, such as databases and Web servers, and cloud platforms, such as AWS and Azure.
After collection, the Log Manager puts log messages into a standard format. This enables messages from different sources that use different layouts to be managed in a unified manner.
Among the messages that the Log Manager receives are logging failures. Checks on the steam of log messages can also highlight problems if the frequency of incoming messages suddenly drops. Under these circumstances, the Log Manager raises an alert and notifies technicians of a potential problem. Those notifications are sent by SMS, email voice call, or instant messaging systems.
The log file system is also useful for compliance reporting and auditing for data security standards.
Site24x7 is a cloud-based service, so most of the components needed to the system, such as the host, are included in the price. One exception to this is the need for an agent to be installed on a server that is part of the monitored system.
The dashboard for the Log Manager is resident on the Site24x7 server and can be accessed through any standard Web browser. The screens offer analysis functions and present log data in visualizations, such as charts and graphs as well as making lists of log records available for viewing.
Who is it recommended for?
It is highly recommended for administrators looking for a versatile cloud-based monitoring tool with a focus on SQL server monitoring, AI-enhanced analysis, and comprehensive application stack insights.
Pros:
- Flexible cloud-based monitoring option
- Offers a host of out-of-box monitoring options and dashboard templates for SQL server
- Allows administrators to view dependencies within the application stack, good for building SLAs and optimizing uptime
- Offers root cause analysis enhanced by AI to fix technical issues faster
- Can unify SQL monitoring across multi-cloud environments
Cons:
- Site24x7 is a feature-rich platform with options that extended beyond databases management, may require time to learn all options and features
Site24x7 Infrastructure, including 500 MB of log processing costs $9 per month when paid annually. Additional log capacity can be added on for: 10GB: – $10 per month, 100GB – $95 per month & 1TB – $900 per month. You can get started with a 30-day free trial.
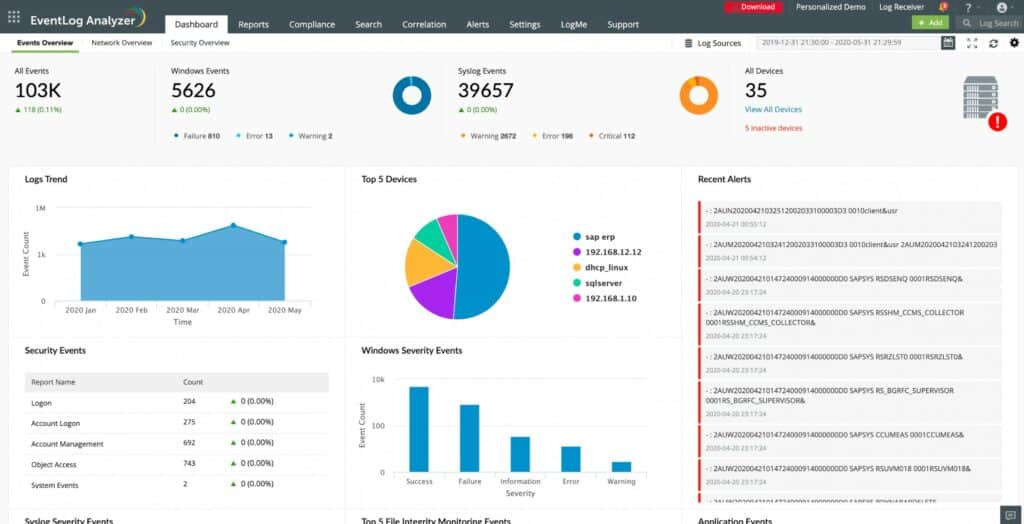
3. ManageEngine EventLog Analyzer – FREE TRIAL
ManageEngine EventLog Analyzer is a web-based, real-time log management and IT compliance solution that combats network security attacks.
Key Features & Capabilities:
- Log Management EventLog Analyzer provides end-to-end log management, with agent and agentless methods of log collection, custom log parsing, complete log analysis with reports and alerts, a powerful log search engine, and flexible log archiving options.
- Application Auditing EventLog Analyzer allows you to audit all your critical application servers.With predefined reports for the applications listed here, the solution also allows you to monitor custom applications. Its powerful custom log parser enables you to easily parse and validate custom log formats.
- Network Device Auditing EventLog Analyzer monitors all your important network devices such as your firewalls, routers and switches.The solution provides predefined reports for all your Cisco routers and switches, as well as firewalls from Cisco, SonicWall, Palo Alto Networks, Juniper, Fortinet, NetScreen, Sophos, Check Point, WatchGuard, and Barracuda.
- IT Compliance Reports EventLogAnalyzer enables you to comply with ease with a variety of regulatory policies, namely PCI DSS, ISO 27001, GLBA, SOX, FISMA, HIPAA, and the newly created GDPR policy.The solution further allows for future needs by enabling you to create custom compliance reports for new compliance policies.
- SIEM With comprehensive log management combined with extensive security features, EventLog Analyzer is a perfect SIEM platform for your network.Security features such as log forensics, threat intelligence, external threat mitigation with auditing of vulnerability scanners and threat applications, make the solution an ideal choice to secure your network and safeguard it against unwanted breach attempts and critical data theft.
- Cross-platform Audit EventLogAnalyzer's reporting console is highly intuitive, with hundreds of predefined reports to meet all your auditing needs, which can be customized, scheduled, and distributed as you require.The reports comprehensively cover the network, including Windows, Unix/Linux, IBM AS/400, cloud platforms, vulnerability management systems, and your critical files and folders.
Why do we recommend it?
ManageEngine EventLog Analyzer is known for its comprehensive log management and IT compliance reporting capabilities, making it an excellent SIEM platform choice for network security.
With comprehensive log management capabilities, EventLog Analyzer helps organizations meet their diverse auditing needs.
It also offers out-of-the-box compliance reports and alerts that meet stringent IT regulatory mandate requirements with ease.
Who is it recommended for?
Ideal for IT professionals seeking a robust log management solution with extensive security features, compliance reporting capabilities, and cross-platform auditing.
Pros:
- Customizable dashboards that work great for network operation centers
- Multiple alert channels ensure teams are notified across SMS, email, or app integration
- Uses anomaly detection to assist technicians in their day-to-day operations
- Supports files integrity monitoring that can act as an early warning system for ransomware, data theft, and permission access issues
- Forensic log audit features enable admins to create reports for legal cases or investigations
Cons:
- Can take a while to fully explore the entire ManageEngine ecosystem
ManageEngine offer a 30-day free trial on the EventLog Analyzer!
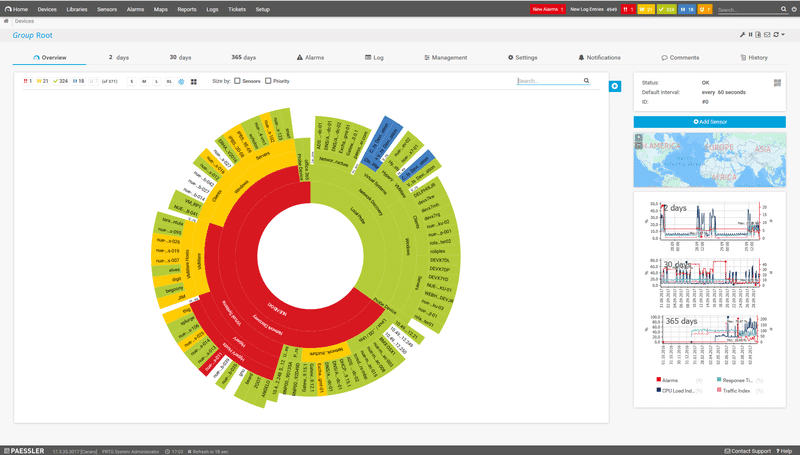
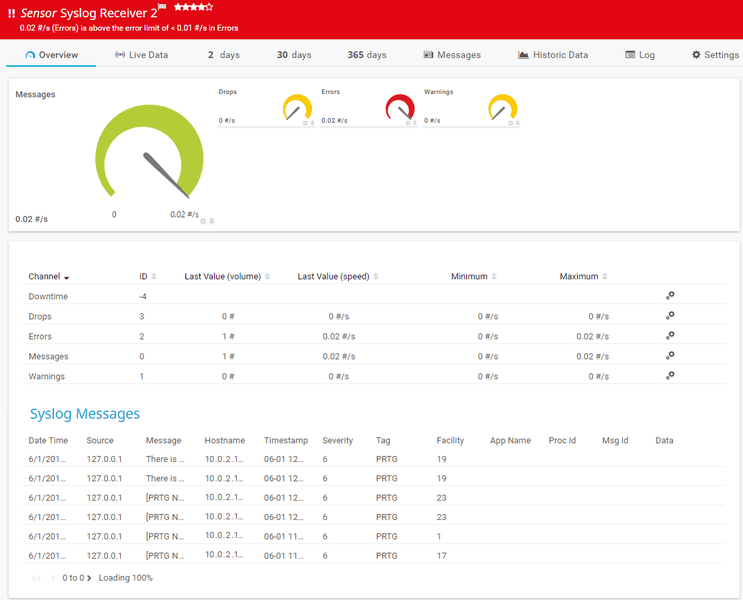
4. PRTG Log Monitoring
Paessler has created a high-performance log monitoring tool that forms part of its PRTG Network Monitor offering. It allows users to identify weak points within their network, and also allows for system administrators to receive alerts directly from the application. It has fully functional windows event log management capabilities, and can also act as a syslog receiver monitor.
Key Features:
- Windows Event Log Management
- Syslog Receiver Monitor
- Customizable Alarms
- Real-Time Network Monitoring
Why do we recommend it?
PRTG Log Monitoring excels in providing detailed and customizable monitoring of network logs, offering valuable insights into system performance and security.
PRTG allows system administrators to assess the level of detail that they require from their logs, and then allows them to apply specific filters to accomplish the task that is needed.
PRTG also has some great reporting capabilities as well, which allows for some impressive graphical representations, such as graphs and charts.
Visualizing this data can make a huge difference when trying to make sense of massive data dumps from system logs.
PRTG is a centralized tool that lets you keep an eye on your most important logs, and also performs some critical real time monitoring across your network as well.
These include servers, bandwidth across the network and applications.
This means that you can act on alerts and then go into the system logs as soon as problems are detected, thereby reducing down time and increasing productivity.
All of these elements make PRTG more than just a mere logging tool, but a critical monitoring and alerting platform as well.
The customizable alarms and personalized dashboards make this a logging tool that can be molded to fit your company’s specific requirements, and not the other way around.
Who is it recommended for?
This tool is best suited for system administrators who need comprehensive log management with a focus on real-time monitoring, especially in Windows-based environments.
Pros:
- Drag and drop editor makes it easy to build custom views and reports
- Supports a wide range of alert mediums such as SMS, email, and third-party integrations into platforms like Slack
- Supports a freeware version
Cons:
- Is a very comprehensive platform with many features and moving parts that require time to learn
Free for Up to 100 Monitors. You can try out the software free for 30-days.
5. Datadog Log Management
Datadog is a cloud-based SaaS platform that offers a range of IT resource monitoring and management tools. Among the list of Datadog services are two log management systems.
Key Features:
- Machine Learning Enhanced Alerts
- Customizable Dashboards
- Historic Metrics Visualization
- Scalable Across Environments
Why do we recommend it?
Datadog Log Management is commended for leveraging machine learning to enhance alerting and reporting. Its customizable dashboards provide an efficient view of IT assets, making it a top choice for monitoring and managing IT resources.
Datadog Ingest is a log server and log file manager. This will collect the log messages circulating around your IT system and store them into files. The storage of log files is carried out on the Datadog server but you need to install an agent program on your system. Communication between the agent and the Datadog log server are encrypted.
The log server will collect Windows Event messages and Syslog records. It can also gather log messages from a long list of applications. Ingest standardizes the format of these messages so that they can be held in a common format.
Who is it recommended for?
This tool is especially suitable for administrators or Network Operations Center teams who require a flexible, scalable solution for log management across various environments. Its machine learning capabilities make it ideal for dynamic, data-intensive scenarios.
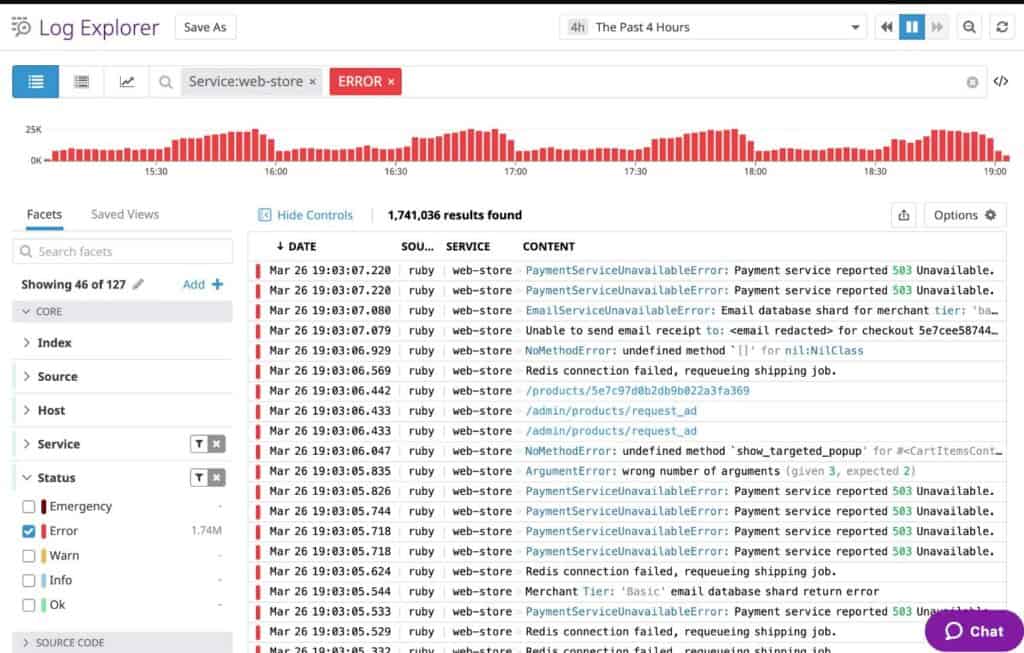
The dashboard for the services shows log messages in a viewer as they get processed into the file. It is also possible to scroll back through the stored records in the viewer. The viewer includes analytical utilities, such as indexing, sorting, and filtering. It is also possible to build your own log message processing systems that select out specific records for further analysis.
The Retain or Rehydrate helps you to manage which log records are available online and which are stored in archives. Available logs are more expensive to maintain, so being able to store archives elsewhere saves a lot of money. Those archives can be brought back on demand when needed, for example, when a compliance audit occurs.
Pros:
- Leverages machine learning to improve alerting, reporting, and queue management
- Excellent dashboards – great for solo admins or NOC teams
- Can easily see historic metrics as well as a live view of your IT assets
- Highly flexible – scales well across various environments
Cons:
- Would like to see a longer trial period for in-depth testing
Datadog Ingest has a charge of $0.10 per GB of processed data per month. Datadog Retain or Rehydrate is priced according to the chosen retention period. A 7-day retention period costs $1.27 per million log events per month. The highest retention period shown in the price list is 60 days and that costs $4.10 per million log events per month. A free trial of either Datadog log management service can be downloaded from here.
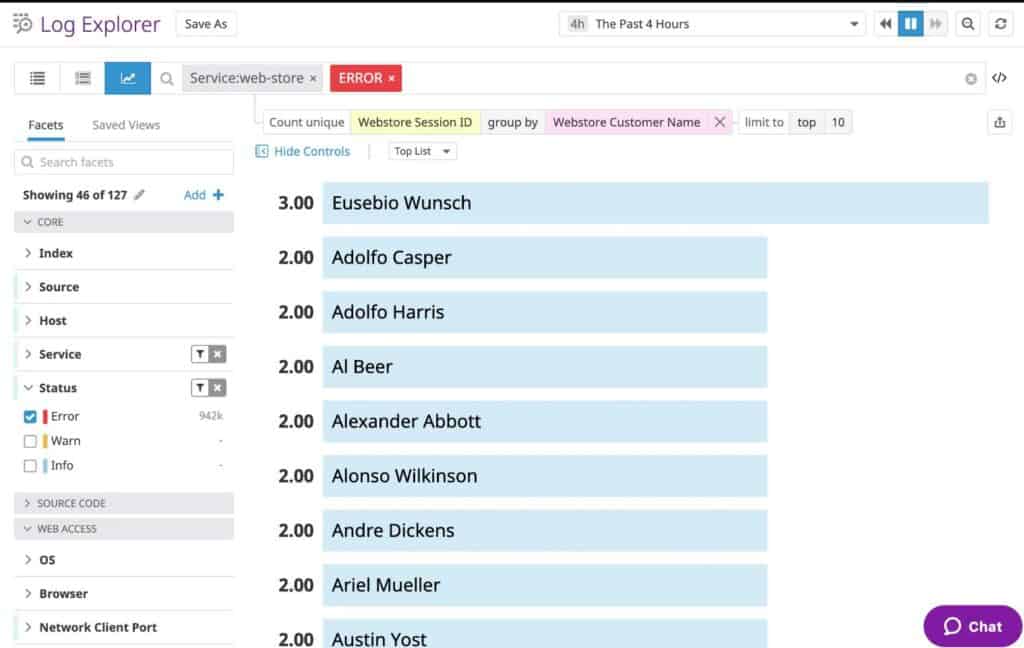
6. Lepide
Event log management in the traditional sense, where administrators manually pore over vast tracts of data by hand, can be very time consuming and difficult.
What made this approach even more difficult is the fact that there are often multiple devices such as servers and desktops that need to be analyzed at once, making the task all the more longer and more difficult. Lepide Event Log Manager seeks to change all of this with some of its great features.
Key Features:
- Event Log Collection and Consolidation
- Advanced Search and Filter Options
- Custom Alert Creation
- Compliance Reporting Capabilities
Why do we recommend it?
Lepide is recommended for its efficiency in log collection and consolidation, along with its advanced search capabilities, making it a practical solution for managing large volumes of logs.
LELM lets you collect logs from multiple sources, and then it allows you to consolidate all of this information into a single resource.
This allows for some quick and valuable insights to be gained in a very short space of time, especially when obvious correlations and trends become apparent.
The application also prevents log overwrites and makes it much easier for system admins to access logs when they need to.
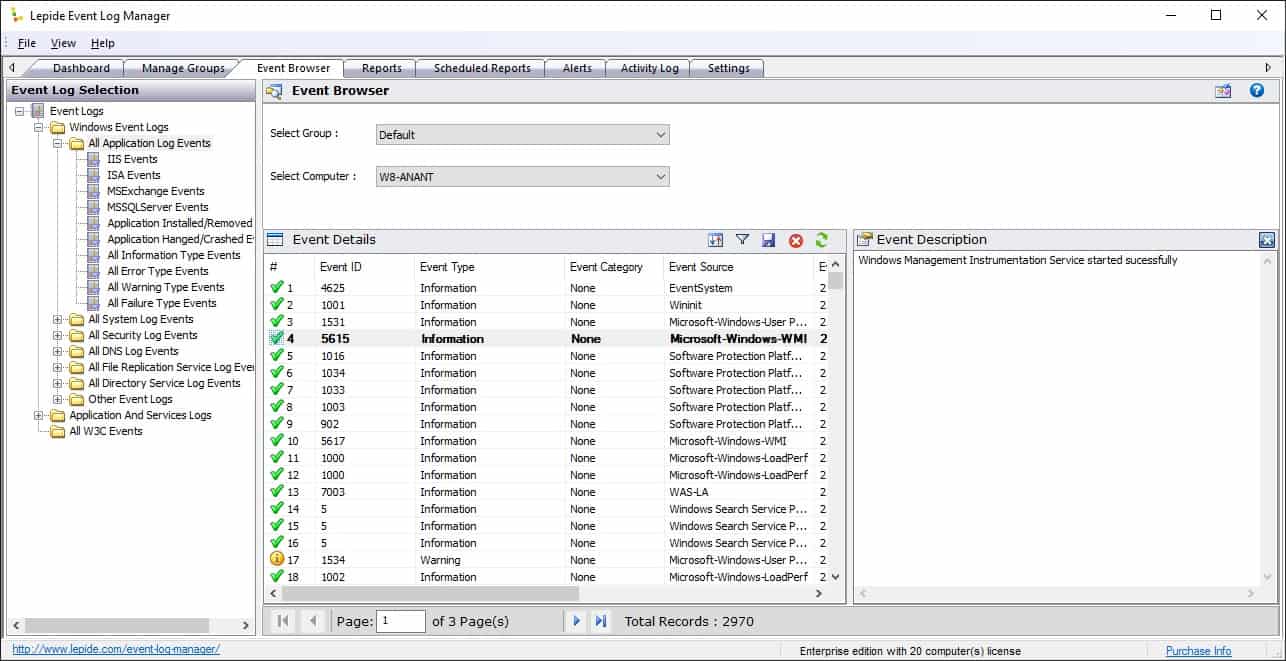
The centralized log repository approach means that they can be accessed by multiple people from multiple locations if necessary, giving your IT department greater flexibility when you need it.
In addition to ease of access, additional search and filter options have been setup to allow for advance log and record searches, saving even more time when logs need to be sorted through.
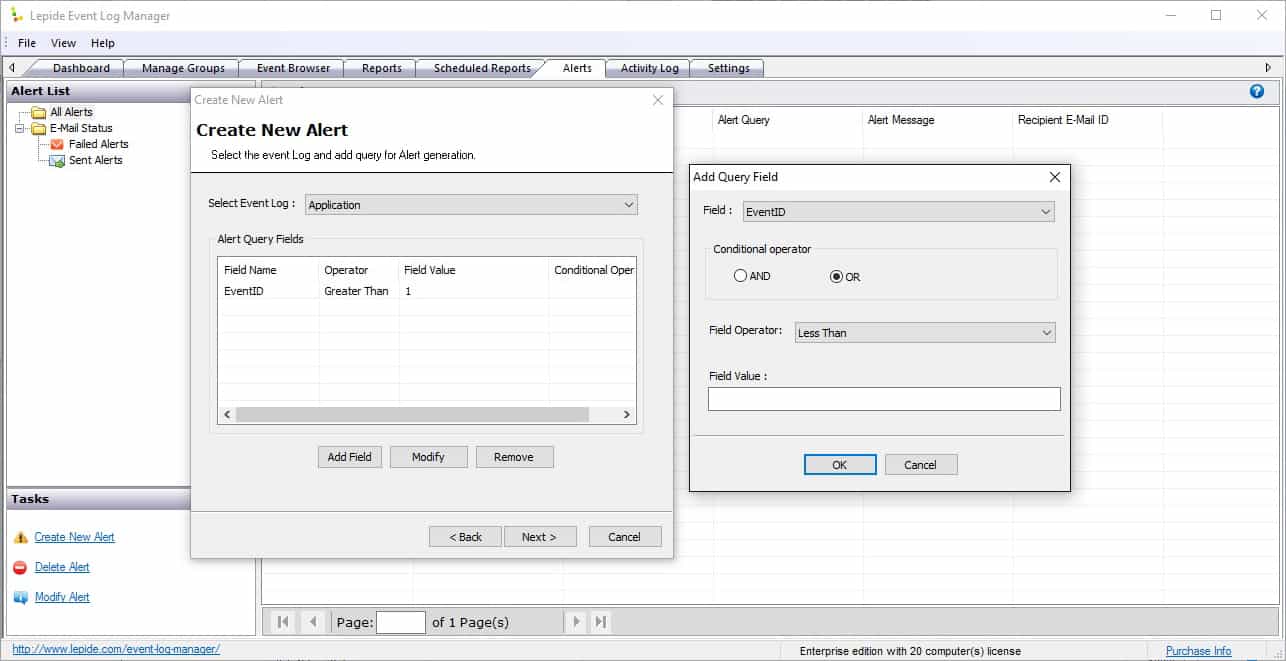
Lepide Event Log Manager also allows users to create alerts, meaning that if any trouble comes up, then your IT department can be kept well informed and on top of any critical errors.
All of these features included make this an ideal log sorting tool and alert monitoring solution.
Compliance is also a great selling point, with ISO, PCI, SOX, HIPAA and GRG13 standards all catered for within the application.
Who is it recommended for?
It's particularly suitable for IT departments requiring a centralized log management system with a focus on compliance and efficient data analysis.
Pros:
- A simple way to see last login, name and CN path of multiple accounts at once
- Can quickly create CSVs or HTML format reports
- Store Windows events in just a few clicks
- A simple wizard makes it easy to set custom threshold-based alerts
Cons:
- Similar tools allow for more functionality like bulk password changes and unlocks
There are currently two versions of the software available: Freeware and Enterprise, which can be downloaded from here. A quotation request form can be filled in here for any pricing queries.
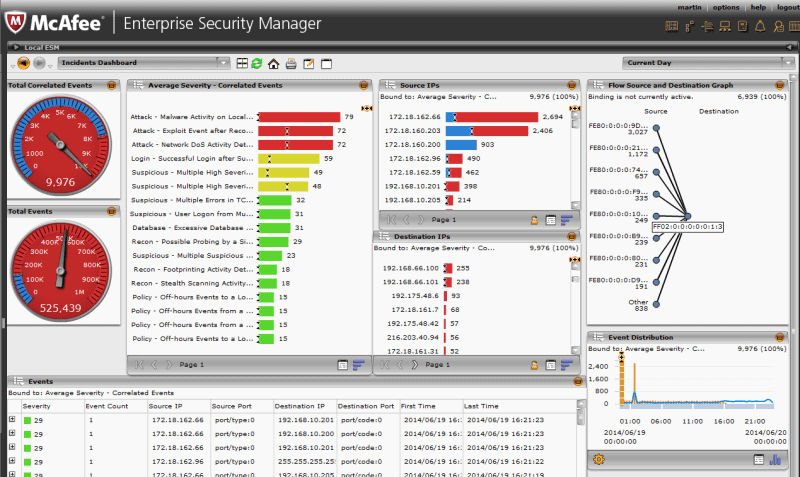
7. McAfee Enterprise Log Manager
McAfee is a well-known brand in the IT world, especially in the Information Security sector, so it should come as no surprise that they also offer an advanced log keeping tool for organizations.
Its main aim is to reduce compliance costs for companies, and to improve efficiency with automated log collection, storage, and management. It is able to do this by collecting, compressing, signing, and storing all original events and activities from your logs, while preserving an audit trail for maximum record authenticity.
Key Features:
- Comprehensive Log Collection
- Automated Log Management
- Compliance Record Segregation
- Network Traffic Monitoring
Why do we recommend it?
McAfee Enterprise Log Manager is notable for its automated log management and comprehensive collection capabilities, facilitating efficient compliance and security monitoring.
McAfee also has a fully comprehensive log collection management function, which offers a universal event log collection and storage system that meets most compliance standards and industry requirements.
This means that it can be used as a means to preserve the chain of custody in forensics investigations and other legal matters.
McAfee understands its enterprise client requirements, and as such offers multiple deployment options to suite a multitude of different operating environments.
They offer physical server installations, as well as VM appliances for virtualized environments.
As well as being able to automate even logs and provide analysis tools, McAfee Enterprise Log Manager also collects logs automatically while storing specific logs for compliance purposes.
It is also able to separate compliance records form analytical ones, creating reports with one set of data, while storing another for record and compliance requirements.
Who is it recommended for?
Recommended for businesses seeking a robust log management solution with strong compliance features, network monitoring, and support for multiple operating systems.
Pros:
- Supports Windows, Linux, and Mac OS
- Offers roll-back points for infected endpoints
- Monitors network traffic to stop DDoS attacks, botnets, and rouge mail servers
- Allows sysadmins to orchestrate security policies across their environment
Cons:
- McAfee can use a lot of system resources while scanning (not ideal for older endpoints)
A free trial can be downloaded from here. Contact McAfee to find out more about pricing, a link to their contact page can be found here.
8. SolarWinds Security Event Manager – FREE TRIAL
SolarWinds has created a log management application that is designed to keep your environment safe, secure and compliant.
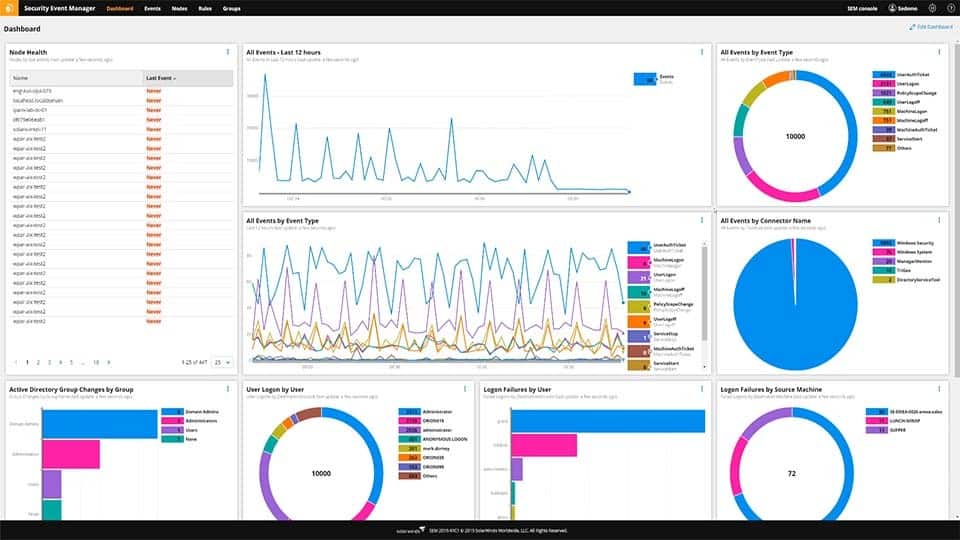
Security Event Manager is a high performance, enterprise grade software suite that helps users to create compliant reports very quickly, making surprise audits that much easier to deal with for your IT department.
Having access to so much information on your network also allows for a much easier time with real time troubleshooting and event correlation.
Finding an error log that corresponds with the timeline of a system failure is an excellent way to seek out issues on your network via the logs, and SolarWinds Security Event Manager are a great example of how this can be achieved quickly, easily, and intuitively.
SolarWinds Security Event Manager has additional features that make it especially handy to have around, such as the ability for operators to detect suspicious activity more quickly, enhanced security threat mitigation, auditable compliance capabilities, and the maintenance and continuation of security, 24/7.
Key features:
- Fast and Easy Compliance reporting
- Real-time event correlation
- Real-time remediation
- Advanced search and forensic analysis
Why do we recommend it?
SolarWinds Security Event Manager is recommended for its robust real-time monitoring and advanced forensic analysis capabilities. It excels in providing fast compliance reporting, essential for organizations needing to meet various regulatory standards.
Security Event Manager (SEM) is a great product that offers many features to keep your log file management in order and maintained easily.

Who is it recommended for?
This tool is ideal for large enterprises and IT professionals seeking a comprehensive solution for real-time network monitoring, event correlation, and forensic analysis. Its advanced features cater well to environments requiring stringent compliance and security measures.
Pros:
- Offers both incident response tools as well as automated remediation and prevention
- Enterprise-focused SIEM with a wide range of integrations
- Simple log filtering, no need to learn a custom query language+
Cons:
- SEM Is an advanced SIEM product built for professionals, requires time to fully learn the platform
It has streamlined compliance with reporting capabilities straight out of the box with: HIPAA, PCI DSS, SOX, ISO, NCUA, FISMA, FERBA, GLBA, NERC CIP, GPG13, DISA STIG, among others.
You can get started by registering for a 30-day free trial.
9. Veriato
Veriato Log Manager is an event and security log management tool that collects information about the servers and computers on your network.
Some of this information is useful for analytical purposes and troubleshooting, while other data sets are kept for compliance and record keeping, allowing companies in certain sectors to remain in line with legislative and legal framework requirements.
Key Features:
- Consolidated Log Reporting
- In-depth Search Filters
- Compliance Report Customization
- Multi-Platform Support
Why do we recommend it?
Veriato is appreciated for its in-depth consolidation features and customizable compliance reporting, making it a versatile tool for various log management needs.
Veriato lets users centralize and consolidate reporting and consolidation tools to track windows server event logs, syslog, and even text log files.
It also has system monitoring capabilities as well, and can monitor Windows, Linux/Unix, routers, switches and other appliances on your network, giving you a powerful overview of what is happening in your environment.
Having multiple data sources means that you can create powerful.
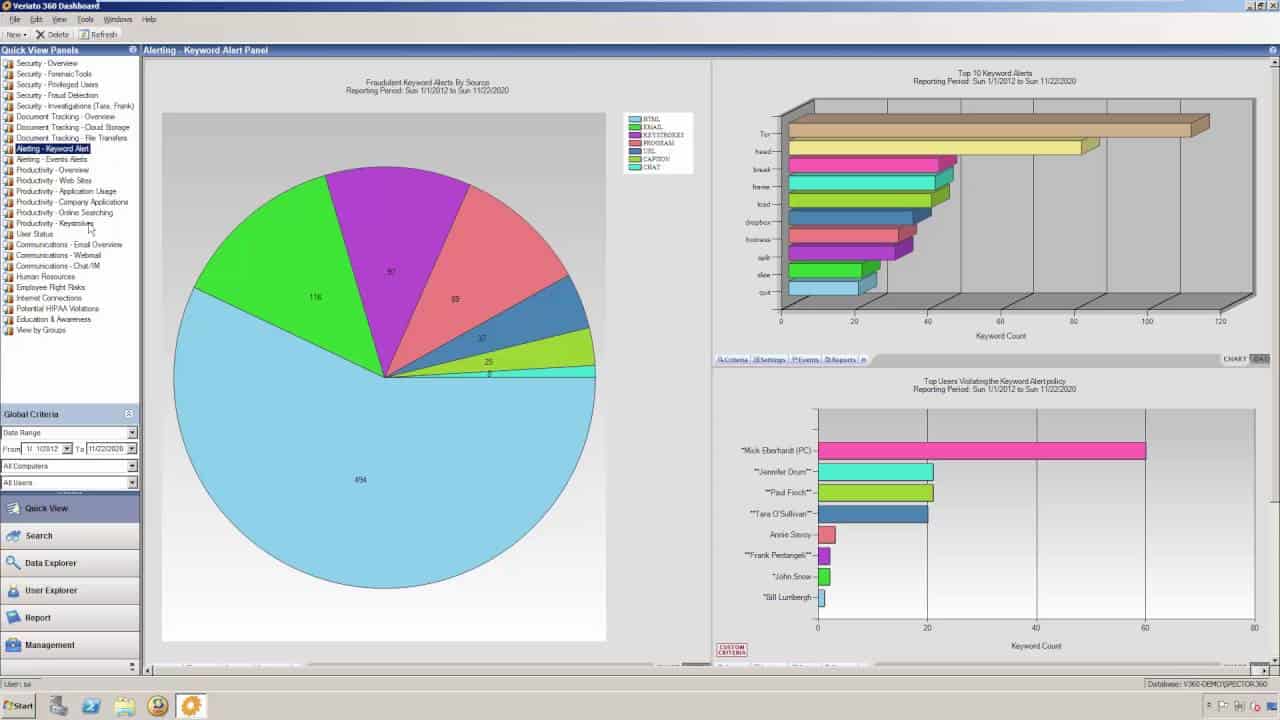
Veriato also offers some excellent graphical views for making sense of your logs, and it can produce some impressive graphs and offers detailed intelligence.
It is able to do this by sorting through only relevant data, and can be further customized to target only specific data metrics that are of interest to your IT department.
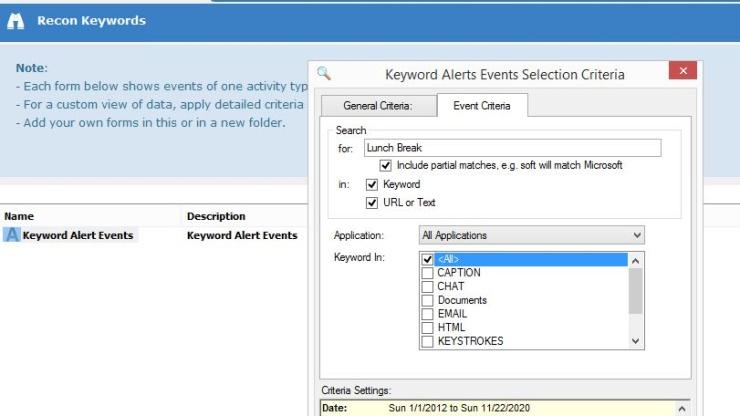
Compliance is also a major feature with Veriato, and these can be customized to suit your specific industry requirements.
They are able to report, record, archive and retireive all of the selected data archives that are set out by your system administrators.
Who is it recommended for?
Ideal for smaller environments requiring detailed log analysis, compliance reporting, and support for multiple platforms including Windows and Azure AD.
Pros:
- Supports log collection from Windows as well as Azure AD
- Provides in-depth consolidation features as well as search filters
- Can run compliance reports for HIPAA and PCI DSS
Cons:
- Better suited for smaller environments, larger networks with 100+ systems may experience slowness
The standards that they are able to comply with are PCI DSS and HIPAA. A trial download can be found on this page. A quotation can be requested from here.
10. Splunk Log Management
Splunk seek to redefine log management software with their product offering with advanced features such as Indexing Machine Data, Search and correlation tools, drill down analysis functionality, as well as monitoring and alert capabilities.
All of this ties in beautifully with their reports and dashboards features. Splunk offers real-time enterprise log and management, with search and diagnostic capabilities built in.
Key Features:
- Advanced Data Indexing
- Real-Time Alerts
- Customizable Dashboards
- Scalable Enterprise Solution
Why do we recommend it?
Splunk Log Management stands out for its advanced indexing and real-time alert capabilities, coupled with highly customizable dashboards, making it suitable for large-scale enterprise use.
This allows Splunk to analyze and index any log data that has been identified as being worth recording, giving your team all the tools that they need to keep track of system errors, and help with advanced troubleshooting.
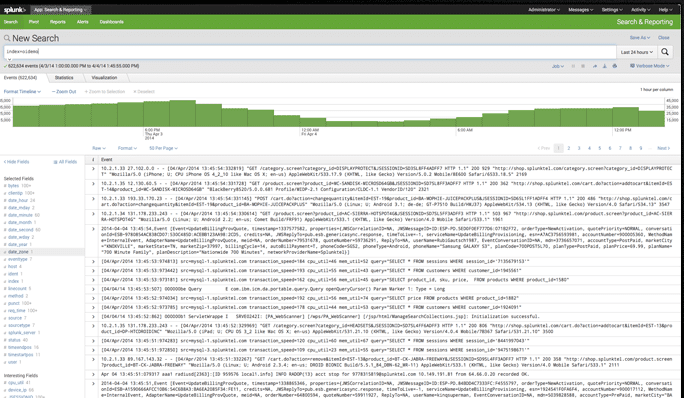
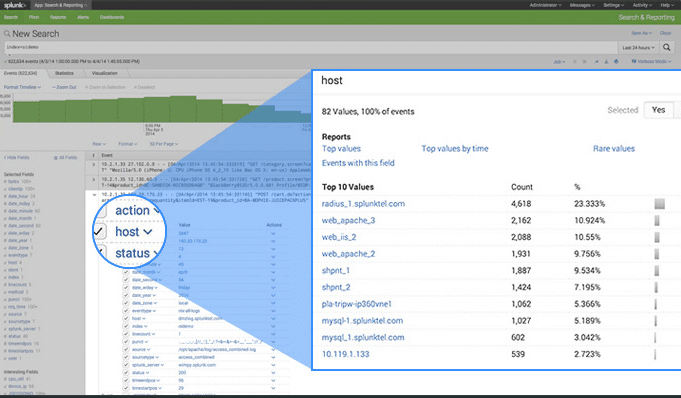
All of these features come together to create a highly effective, and good looking data logging solution.
Splunk performs incredibly well at scale, and can make troubleshooting large problems on the network.
Who is it recommended for?
This tool is particularly beneficial for large enterprises needing a scalable, comprehensive log management solution with a focus on behavior analysis and threat detection.
Pros:
- Can utilize behavior analysis to detect threats that aren’t discovered through logs
- Excellent user interface, highly visual with easy customization options
- Easy prioritization of events
- Enterprise focused
- Available for Linux and Windows
Cons:
- More suited for large enterprises, cost-prohibitive for small businesses
Compliance also plays a large role within the Splunk application, and it is able to keep your records in order to meet these requirements.
A full price guide can be found here.
Conclusion
Keeping an effective logging system is incredibly important for many different reasons:
- Log Tracking
- Alerts & Notifications
- Compliance
The first and probably most important reason is for your IT administrators.
They are able to keep track of issues, troubleshoot and investigate difficult system issues on your network, and without system logs they would not be able to solve many of the complicated problems that are associated with modern networks.
The second important reason is for alerts and real-time notifications. Some of the log keeping software that we have looked at today are able to keep you in the loop about system issues by sending out email alerts whenever specific filters detect logging conditions that trigger a warning or alert notification.
This makes it possible for the systems to act as real time warnings for your IT department to act as quickly as possible.
The third reason is for compliance reasons. Many industries now require that logs be kept in a specific format so that they can be audited and checked for adherence to the prescribed laws and policies that may or may not apply to your specific industry.
There are many different types of compliance regulations that need to be followed, sometimes there are multiple standards for a single company to follow, depending on the industry that they are a part of.
Hopefully you have gained some insight into the different products that are available on the market today, and that you can make an informed decision based on our review.