Being aware of the threat in your environment is very important to cybersecurity teams. Cyberattacks and Advanced Persistent Threats are all on an upward trend, giving Information Technologies many additional challenges to consider around security.
Collecting threat data has resulted in information overload in many cases, and companies are not necessarily getting value from all of the different data points relating to threat data. In an effort to combat this phenomenon many businesses have deployed Threat Intelligence platforms as a means to track, manage and combat cyber threats.
Here is our list of the best threat intelligence platforms:
- Datadog Security Monitoring This SIEM system includes a threat intelligence database that is gathered from all subscribers to the security package. This is a cloud-based service.
- CrowdStrike Falcon X This cloud service produces a range of threat intelligence formats that are particularly tailored for use with the CrowdStrike Falcon stable of security products.
- Anomali Threat Platform This cloud-based protection system will work with a list of threat intelligence providers, You select an option from the Anomali App Store and pay a separate subscription for it.
- Cisco Talos this group maintains the threat hunting rules for a range of Cisco security products, including Snort. The team produces threat intelligence in a range of formats.
- Digital Shadows SearchLight This threat intelligence service comes from a provider of security consultancy services and includes Dark Web intel as well as vulnerability and IoC feeds.
- Mandiant Advantage Platform This subscription service gives you access to a menu of intelligence that includes industry information and an automated feed that you can set for periodic download.
- Infoblox Threat Intelligence Unit This department of cybersecurity consultants gathers intel from many organizations, producing a feed and also reports from that data.
- Heimdal Threat Hunting and Action Center A cloud-based threat detection and automated response system that shares threat intelligence around a private network to promote system preparedness.
- LookingGlass Scout Prime This is a tailored intel service that includes Dark Web sweeps for data leaks of PII that impact your business.
- Recorded Future Subscribers to this platform get access to databases of different threat intelligence that can all be linked together and automatically extracted on a schedule as a feed.
- Webroot BrightCloud Threat Intelligence Services A threat intelligence feed that gets instantly plugged into your system through APIs and one-click integrations.
Most businesses, if not all, are vulnerable to the current generation of cybercriminal activity.
The most visible threats are ransomware, DDoS, Zero-Day attacks and many other constant threats that could be described as APTs.
Smaller businesses are especially at risk because most do not have a well-defined security plan in place to ensure that they can combat these threats effectively, leading to increased vulnerability. Part of this is because of the prohibitively costly outlay that a proper security plan and cyber threat detection and elimination system come with.
However, the vast majority of security-conscious SMBs are putting safety measures in place to protect their data and digital systems.
As a result, the threat intelligence segment is forecast to grow by staggering margins, making the sector a very well-developed one.
This means that many more competitors are beginning to come to the market with innovative and impressive products, which gives business consumers more options than ever before.
With this in mind, we will be delving into the current state of the market so that we can evaluate some of the current generation products that are finding their way onto corporate networks.
The Best Threat Intelligence Platforms
Our methodology for selecting threat intelligence platforms and software
We reviewed various threat intelligence platforms and analyzed the options based on the following criteria:
- Support for various operating systems and network environments
- Support for muti-tenant features
- Auditing, alert, and reporting capabilities
- A facility to analyze, monitor and alert on threats overtime
- Graphical interpretation of data, such as charts and graphs
- A free trial period, a demo, or a money-back guarantee for no-risk assessment
- A good price that reflects value for money when compared to the functions offered
1. Datadog Security Monitoring

Datadog Security Monitoring is a threat intelligence system that uses SIEM techniques to hunt for threats. This system is based in the cloud and benefits from the central threat intelligence database held by Datadog.
The Datadog system processes all data on cloud servers but requires data-gathering agents to be installed on the systems to be protected. This can be a site or a cloud platform. The data collectors gather log messages and output from standard system monitoring services, such as SNMP for network device operations. This collected data is uploaded to the Datadog servers.
Key Features:
- Cloud-based SIEM techniques
- Central threat intelligence database
- Layered threat detection process
- Customizable cloud console
Feature distinction
It combines traditional security practices with the performance and application data to provide holistic views.
Why do we recommend it?
Datadog Security Monitoring is a powerful cloud-based system that uses advanced SIEM techniques for effective threat hunting. Its central threat intelligence database and layered detection process make it highly efficient in identifying and responding to threats.
Datadog’s Security Monitoring system standardizes all of the messages that it receives from collectors so that they can all be held in a common format. The assembled pool of messages is available to the threat-hunting system of the security monitoring service.
The threat detection module applies rules that are supplied by the central Datadog threat intelligence database. These records of things to look out for are called Indicators of Compromise (IoCs). Threat detection is a layered process. The Datadog system doesn’t raise an alert when one of its IoCs identifies malicious activity – this might just be a normal transaction that accidentally happens to match an IoC.
The system looks for chains of activities that represent a threat. Thus, if one indicator is discovered, the threat detection system looks out for another event that reinforces suspicions. Some IoCs require immediate action, such as large amounts of data being moved or log files being altered. Other actions will only represent a threat if they are combined with other actions. So there is no standard template for an IoC.
The standard Security Monitoring package from Datadog is suitable for use by IT Operations departments. The tools can merge the monitoring of several sites and also mix in the supervision of cloud resources. Thus, it is possible to impose security monitoring from one central location.
The console for the Datadog Security monitoring unit is based in the cloud and can be customized. Administrators can access the system through any standard Web browser. The Datadog system includes a series of alerts that will trigger notifications to key members of the team. You choose who gets notifications for different types of threats and you can also choose how those notifications are delivered.
The alerting mechanism in Datadog Security Monitoring frees up staff for other tasks because it isn’t necessary to allocate one technician to sit and watch the monitoring console all the time. Datadog offers other security services that add up to an entire security services platform. These other tools are needed by developers and DevOps teams.
The platform includes vulnerability scanners and continuous testing systems. There is also a code profiler that can be plugged into the security monitoring system to identify which lines of Web application code represent a security risk.
Through “integrations,” Datadog Security Monitoring can exchange information with third-party software. This enables the monitor to gather extra activity data and also to feed through responses and solutions so that they can be automatically implemented by other systems.

Who is it recommended for?
Ideal for IT operations departments that require a unified security monitoring system capable of overseeing multiple sites and cloud resources from a central location.
Pros:
- Offers numerous real user monitors via templates and widgets
- Can monitor both internally and externally giving network admins a holistic view of network performance and accessibility
- Changes made to the network are reflected in near real-time
- Allows businesses to scale their monitoring efforts reliably through flexible pricing options
Cons:
- Would like to see a longer trial period for testing
All Datadog modules are subscription services and they can be used individually or in combination. It is possible to source all of your system monitoring tools from the platform to watch over networks, servers, and applications. Datadog offers a 14-day free trial of all of its services.
Official Site: https://www.datadoghq.com/dg/security/threat-intelligence/
2. CrowdStrike Falcon X
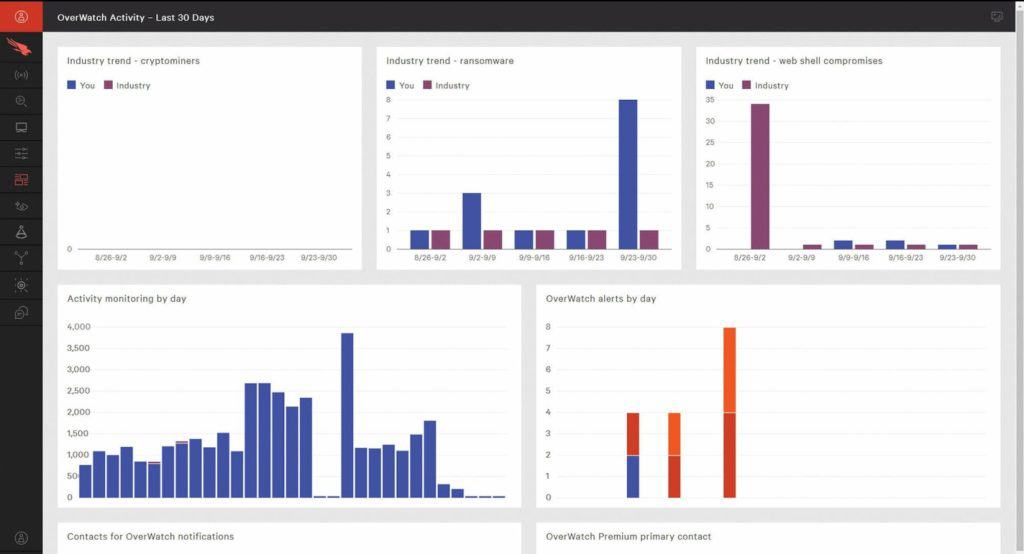
CrowdStrike Falcon X is another threat intelligence platform that seeks to integrate with endpoint protection and automated incident investigations. This speeds up the overall incident response and investigation process and is a valuable tool for your cybersecurity team.
The product offers instant threat analysis as each threat reaches your endpoints on the network as well as collaboration with the global CrowdStrike Falcon Intelligence team. The overall process helps to enable a predictive analysis model, which is good news for information security professionals.
Key Features:
- Instant threat analysis
- Custom Indicators of Compromise
- Expert support from CrowdStrike
- Endpoint integration and malware analysis
Why do we recommend it?
CrowdStrike Falcon X provides rapid threat analysis and predictive analysis models, backed by CrowdStrike's expert team. Its capabilities in custom indicators orchestration and malware analysis make it a comprehensive solution for cybersecurity.
Falcon X offers a few other compelling features that make it an ideal choice for any enterprise that is looking to button down their security and strengthen their cyber security protection efforts. They are:
- Threat Intelligence This is the automatic investigation component that all incidents pass through, allowing the system to learn from all attacks that occur on the network and within your environment. These threats are then analyzed very quickly, usually within minutes, which lets users of the software respond much more quickly.
- Custom Indicators Orchestration is an important aspect of any cyber security effort, and FalconX allows for custom indicators to be used in this process. Indicators of Compromise (IOC) are generated by threats, which are then used to mount an active defense against attacks that might come in the future.
- CrowdStrike Expertise Having professional support is vital in cybersecurity, so CrowdStrike makes their teams available to their customers. There are threat analysts, security researchers and cultural experts and linguists that all work together to provide you with a solution that helps to identify and neutralize threats much faster than conventional standalone systems.
Falcon X has many other features that are especially useful in a cyber security context, such as:
- Endpoint Integration All files that get quarantined by CrowdStrike can also be automatically investigated by Falcon X if it is configured in this way.
- Threat Intelligence In order to successfully deal with an attack, there needs to be an understanding of who is carrying it out. Threat Intelligence is there to help identify and predict future attacks based on information from past and present ones.
- Malware Analysis File analysis is done within Falcon’s Sandbox environment so that no damage can occur to external systems. A full range of tests are performed on the malware instances that are sent to this environment so that all information about the instance can be learned.
- Malware Search Being able to automatically discover threats is crucial in complicated network environments that span many different locations. Falcon X helps to find related instances and campaigns of malware, which it then uses to help defend against future attacks.
- Custom Intelligence FalconX generates custom IOC data for threats that your system has already dealt with. From this information it generates information about threats that you are likely to encounter going forward. This information can also be shared with other systems so that added protection is available where FalconX cannot be installed.
Other features include weekly threat reports, actor profiles and indicators, threat orchestration and cloud-based architecture.

Who is it recommended for?
Best suited for enterprises that require a holistic approach to cybersecurity with rapid threat analysis and expert support for incident investigation.
Pros:
- Doesn’t rely on only log files to threat detection, uses process scanning to find threats right away
- Acts as a HIDS and endpoint protection tool all in one
- Can track and alert anomalous behavior over time, improves the longer it monitors the network
- Can install either on-premise or directly into a cloud-based architecture
- Lightweight agents won’t slow down servers or end-user devices
Cons:
- Would benefit from a longer trial period
Trial: You can begin with a 15-day free trial.
Download: https://www.crowdstrike.com/products/threat-intelligence/falcon-x-automated-intelligence/
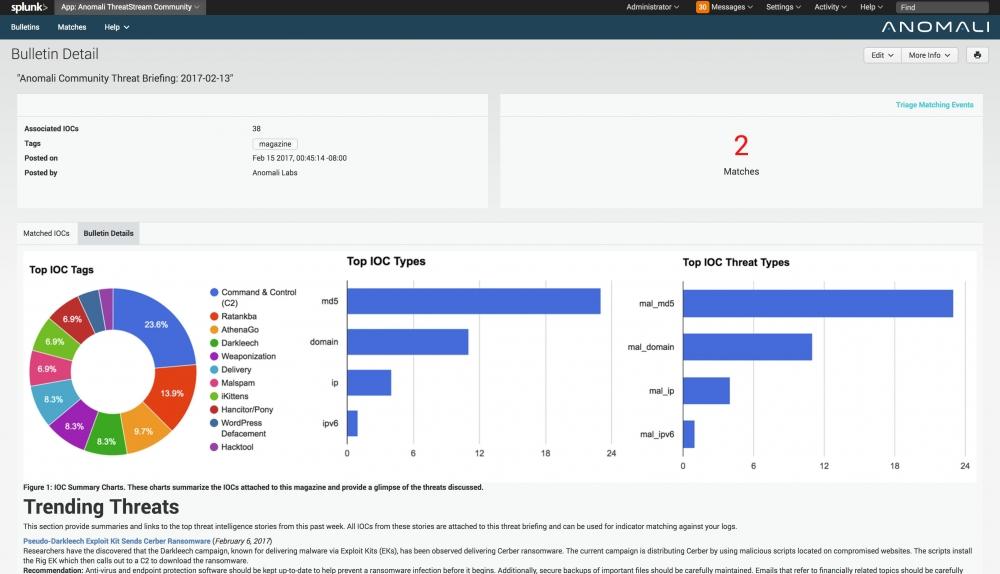
3. Anomali Threat Platform
Anomali Threat Platform is a system that is built on the premise that it is better to know who your enemies are than it is to randomly protect yourself from unknown threats. Anomali uses advanced threat detection at the core of its product, and this helps it to defend your network against intruders and malware.
It gives your security team the ability to collect and analyze data from multiple feeds such as OSINT, STIX/TAXII, ISACs. You only need to use the feeds that you want, meaning that you can purchase additional feeds from the Anomali APP Store as and when the need arises.
Key Features:
- Collects and analyzes data from multiple feeds
- Machine Learning for reducing false positives
- Centralized view for threat intelligence
- Historical data comparison for trend analysis
Why do we recommend it?
Anomali excels in aggregating threat data from various sources, offering a centralized platform for analysis. Its use of machine learning to reduce false positives and capability to analyze historical data make it highly effective in threat detection and trend analysis.
Another powerful tool in this security stack is the product’s Machine Learning feature. This allows your team to leverage advanced threat intelligence which has the added benefit of reducing false positives.
The way that Anomali gathers and normalizes data from multiple sources means that you can have a single point and source of information while accepting multiple feeds from different systems. This gives you a centralized view of the current threats on your network and will ultimately allow you to have the visibility that you need to monitor and evaluate your organization’s current vulnerability state. This gives security analysts a true advantage as they are able to quickly and easily observe the data in a single view.
Threat detection is another area where this product starts to shine. Anomali is able to apply a weighted scoring algorithm to the gathered data and ultimately makes it easy for you to rank the most serious threats in order. This allows for a more effective threat response.
On top of standard threat detection Anomali is able to look at the historical data that you gather and compare it to new threats that are identified. This can help you to establish trends and historical data and measure it against past incidents.
Anomali can also be integrated into your current stack, which is an additional layer of security to your security measures. Detection is also assisted through the use of some of the best threat intelligence sources available. This is also customizable so that you can iteratively arrange your response patterns.
Automation is another huge part of this platform's appeal, as many of the detection and reporting steps are done without human intervention. This means that all the repetitive and tedious tasks can be set up to run on a schedule, or whenever they are needed.
This eliminates the need to evaluate and standardize your massive payloads of threat data, which saves time. You can add additional insight to each of the indicators in order to enrich your data collection efforts. You can also greatly strengthen your workflows by integrating them with your existing orchestration platforms.
Further integration is therefore possible with SIEM and EDR solutions as Anomali allows for enhanced alert generation through integrations. This helps with prioritizing and alerting your teams about any potential incidents and breaches. You can also actively block high severity threats through integrations with FW and IPS.
Who is it recommended for?
Ideal for organizations looking for a comprehensive threat intelligence solution that offers a unified view of threats and an effective way to analyze and respond to them.
Pros:
- Highly flexible platform
- Offers a free cloud-based intelligence feed
- Offers threat detection as a service
Cons:
- Better suited for medium to large-sized companies
For further information be sure to request a demo here, and a vast array of information can be found in their resources section.
Official Website: https://www.anomali.com/
Download/Trial: https://www.anomali.com/request-a-demo
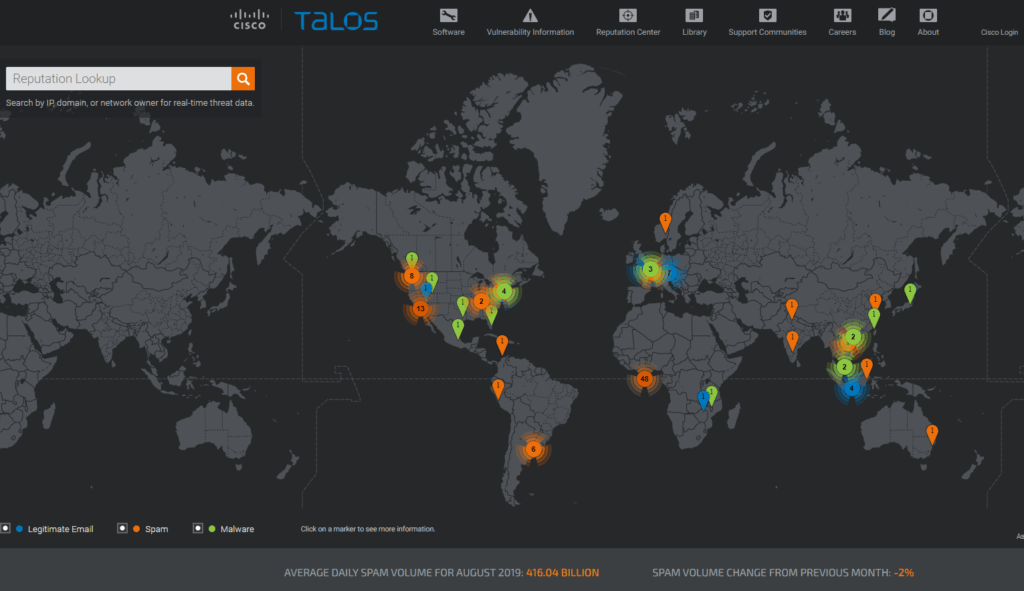
4. Cisco Talos
Cisco’s Talos Security Intelligence and Research Group is a collective of professionals that perform some of the world’s foremost threat research. They have advanced systems at their disposal to help create some of the world’s most advanced threat detection systems.
It plugs into Cisco’s existing technologies and helps to detect, analyze and protect against both known and upcoming threats. Talos is responsible for maintaining the rule set for snort.org, ClamAV, SenderBase.org and SpamCop, so its acceptance in the market is massively apparent.
Key Features:
- Global threat research and monitoring
- Maintains several major security databases
- Variety of specialized security tools
- Supports open-source security tools
Why do we recommend it?
Cisco Talos stands out for its global threat research and monitoring capabilities. With its maintenance of major security databases and support for various specialized and open-source tools, it offers a vast array of resources for enhanced cybersecurity.
Talos is slightly different to the other software products that we will be looking at today, mainly because it is not a single application. Instead, it is a series of tools and professionals that are able to assist their customers with advanced threat detection and management.
Each of the following tools listed are available from their website here and can help you to understand the kinds of threats that they are there to help you with.
They are:
- Snort An open-source intrusion prevention system that also acts as a real-time traffic analyzer and packet logger.
- Daemonlogger This is a barebones packet logger that allows users to soft tap on NSM network environments.
- ClamAV This is an open-source antivirus engine that is really good at detecting trojans, viruses and malware, as well as other malicious threats.
- Moflow This is a software security framework that contains an assortment of automated tools that allows for vulnerability scans.
- PE-Sig This tool is for analyzing and detecting PE section hashes associated with executable files. It feeds into ClamAV and lets you create simple ClamAV-based signatures.
- Immunet This is a malware protection system that uses cloud computing and social networking sources to help plug security gaps with community security.
- Synful Knock Scanner This is a network scanner that detects SYNFul Knock router malware and alerts you of what to do if your systems are infected.
- TeslaCrypt Decryption Tool This is an open-source command-line tool that is used for decrypting TeslaCrypt ransomware.
- MBR Filter This is a Disk filter that blocks access to a hard drive’s Master Boot Record, which is where certain types of malware write themselves to avoid detection and to propagate themselves.
- Thanatos Decrypter This is another decryption tool that is to be used via the command line to decrypt files affected by Thanatos ransomware.
- FIRST Also known as Function Identification and Recovery Signature Tool, this is an IDA Pro plugin that is used by reverse engineers.
- LockyDump This is another open-source tool that lets users extract Locky configurations and dump them to a file location. This has all known variants of Locky covered, such as .locky, .zepto and .odin based ransomware.
There are many more tools available via the Cisco Talos website, as well as a very detailed blog, which covers the current state of information security as it relates to new threats and trends within the information sector.

Who is it recommended for?
Best suited for large organizations, particularly those already using Cisco hardware, looking for comprehensive, expert-backed cybersecurity support and resources.
Pros:
- Enterprise-focused group of security experts monitoring threats across the globe
- White glove service – better suited for larger companies
- Leverages Cisco’s market presence to collect live threat data
Cons:
- Best for those already using Cisco hardware
More information about this invaluable resource can be found here.
Official Website: https://talosintelligence.com/
Download/Trial: https://talosintelligence.com/software
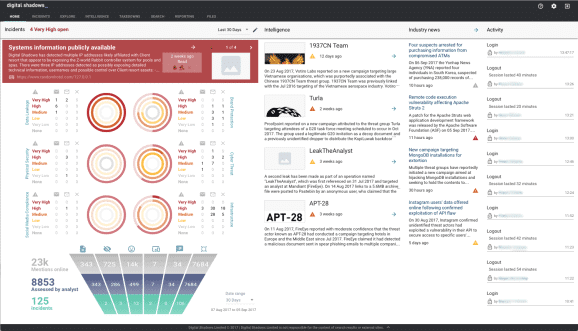
5. Digital Shadows Shadow Search
Digital Shadows is a company that specializes in digital security. They offer a wide range of products such as Phishing Protection, Dark Web Monitoring, Account Takeover Prevention, Threat Intelligence, Data Leakage Detection, and Digital Footprint Monitoring.
Digital Shadows Searchlight is part of the Threat Intelligence solution that they offer. It protects against threats that are external to your site, and it runs on a continual basis. It provides you with the context that you need in order to properly understand the risk as well as your next course of action in order to remediate the situation and neutralize threats.
Key Features:
- Comprehensive external threat protection
- Monitoring across internet and dark web
- Real-time curated threat intelligence
- Customizable alerts and playbooks
Why do we recommend it?
Digital Shadows Shadow Search provides extensive monitoring capabilities, covering the internet and dark web. It offers real-time, curated threat intelligence and customizable alerts, making it effective in identifying and mitigating external threats.
What makes Searchlight different from other solutions that are available on the market is the fact that it is so widely used. Another aspect to consider is the fact that there are many different disciplines that the solution provides protection from.
It offers wider coverage across the internet, and the dark web. This allows it to draw from many other sources, giving deeper context to the threat intelligence that it is able to gather. SearchLight is customizable so that only the most relevant information is available for you and your team.
They have partnered with businesses such as Splunk, ServiceNow, Symantec, Anomali, and Cisco. SearchLight works by first identifying the key assets of your environment. They need to understand what is most important to your operational needs, so this is the best place to start.
It helps to keep only the most relevant information flowing to your systems and staff so that they can make better decisions when dealing with threats. SearchLight is able to search across multiple data sources to find out if any key information is being shared about your organization such as usernames, passwords, and even code related to your internal applications.
Any information relating to your company and systems that trigger the alert system can be customized so that your teams are notified whenever a positive result occurs. A lot of data is collected by the system, so context is very important for the effective filtering of information for your teams.
SearchLight is able to flow the rules that have been set up so that only the most important and impacting information is made available to the right teams. Once a scenario has been identified that requires action a playbook is launched.
This can trigger events such as website takedown requests where sensitive data is being shared. The datasheet covers a lot of technical specifications relating to the application, including how to minimize risk to your business, as well as what the critical components of your threat intelligence solution should be comprised of.
Who is it recommended for?
Recommended for organizations seeking a proactive approach to cybersecurity with a focus on external threat monitoring, including digital footprint and dark web activities.
Pros:
- Can protect image copyright and trade secrets
- Looks for usernames, passwords, and other indicators of compromise
- Uses visualizations to help highlight key insights
Cons:
- Only offers a seven-day trial
- Lack remediation tools
For more information and to request a demo be sure to check out the link here.
Official Website: https://www.digitalshadows.com
Download/Trial: https://info.digitalshadows.com/DemoRequest-Website-Button.html
6. Mandiant Advantage Platform
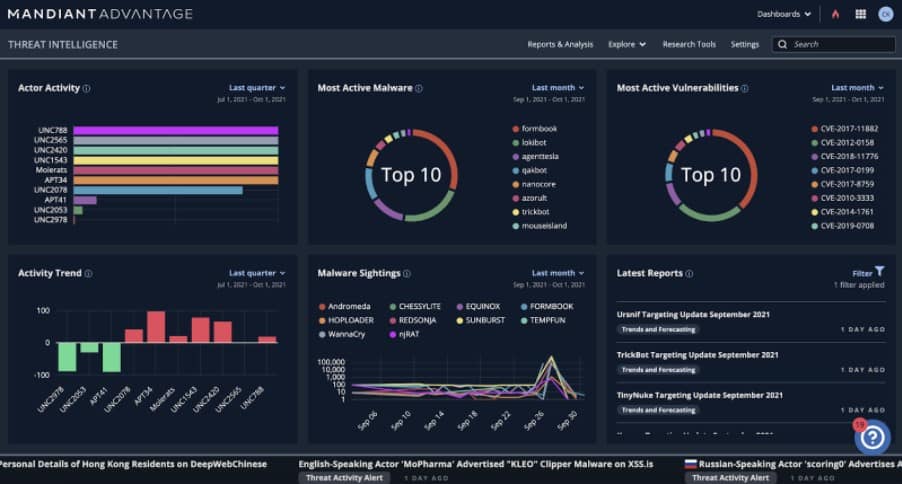
Mandiant Threat Intelligence is a subscription service. Account holders get access to a cloud-based dashboard that offers a range of information pages that range for industry alerts and tips on threat management.
The platform includes a threat intelligence database that is constantly updated and subscribers can specify an extract period to get updates sent as downloads to their existing security software.
Key Features:
- Access to a continuously updated threat database
- Customizable threat intelligence feeds
- Searchable database with analytical tools
- Four types of threat intelligence
Why do we recommend it?
Mandiant Advantage Platform offers a comprehensive, continuously updated threat intelligence database. Its customizable feeds, searchable database, and multiple types of intelligence provide a versatile tool for forward planning and risk assessment.
The database access allows you to specify which type of data gets included in your threat intelligence feeds. This enables you to filter records so that they are only those details that are relevant to your business. For example, you would look for data that relates to your location and industry and well as general universal threat data.
The database is searchable and the platform offers analytical tools, so you can use the system to identify areas of your system that might breed hardening. You can also identify areas of businesses or places in the world that prevent a higher risk and use that information to decide whether it would be better to withdraw from that market rather than risk the profitability of your entire business.
The Mandiant system can also be used for forward planning, helping you decide what risks are involved in signing new contracts or opening a presence in new markets. The Mandiant system provides four types of threat intelligence:
- Breach Intelligence
- Adversary Intelligence
- Machine Intelligence
- Operational Intelligence
This is one of the most comprehensive threat intelligence services in the world. For example, its Machine Intelligence service logs up to 70,000 new attacks every hour.
Mandiant recently split for FireEye. The Mandiant business focuses on its Threat Intelligence, Managed Defense services, and Threat Response consultancy. FireEye still produces security products. As these two companies were, until recently one organization, all of the Mandiant feed formats are particularly suitable for FireEye products.
Who is it recommended for?
Ideal for organizations looking for a detailed, cloud-based threat intelligence service with customizable options for targeted intelligence gathering.
Pros:
- Simple cloud-based subscription service
- Includes continuously updated threat intelligence
- Powerful search queries and syntax
- Includes a free version
Cons:
- Best for companies looking to manage their security internally
There are three plan levels for the Mandiant Advantage Platform. The first of these is Free. This gets you access to threat notifications and industry news. To get a threat intelligence feed, you would need to take out one of the two paid plans, which are called Security Operations and Fusion.
Official Website: https://www.mandiant.com/advantage/threat-intelligence
Sign up for a Free account: https://www.mandiant.com/advantage/threat-intelligence/free-version
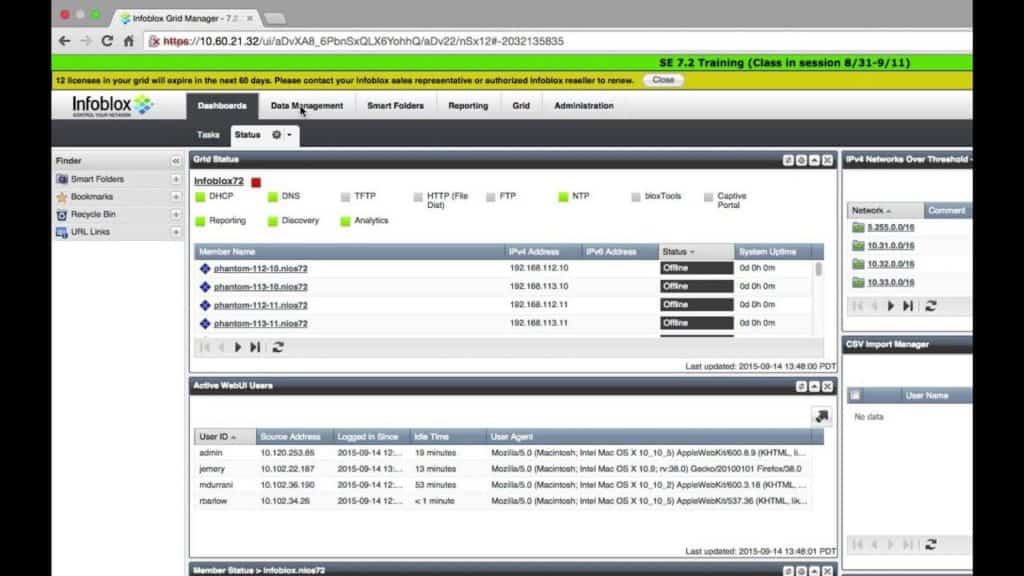
7. Infoblox Threat Intelligence Unit
Infoblox Threat Intelligence Unit gives you access to real-time threat data. It allows you to stop threats with a better turnaround time and is accurate with massive data sources. It will help you to minimize the risks to your business by protecting your infrastructure against cyberattacks.
Their data is sourced from many different areas, such as leading threat intelligence providers, government agencies, the Department of Homeland Security’s Automated Indicator Sharing (AIS) system as well as universities. The system is easy to use for your security team and gives your responders a single interface that they can work from. This makes it much easier to distribute Infoblox’s information throughout your organization to help combat cyber-crime.
Key Features:
- Real-time threat data from multiple sources
- Unified interface for responders
- Cyber Intelligence Unit for additional insights
- Continuous monitoring including third-party vendors
Why do we recommend it?
Infoblox's Threat Intelligence Unit offers real-time threat data aggregation from a variety of sources, providing a unified interface for effective response. Its continuous monitoring, including of third-party vendors, provides comprehensive coverage.
The end result is that your security teams will be able to leverage hundreds of thousands of valuable indicators that are published daily. This means that your team will be current and up to date with the most recent threats that have surfaced within the present time.
It also helps to reduce time to solving and remediating issues, sometimes by as much as two-thirds faster. It will help to make your team three times more effective y leveraging multiple sources of data and using automated tasks to increase speeds and efficiencies within your organization. By unifying your security policies, you can share curated threat intelligence in real-time, giving your teams much-needed and increased visibility.
These integrations include systems such as firewalls, web proxies, SIEM and SOAR platforms. All of this information helps your decision-makers and teams get all of the most important information as and when it is needed. You can also gain valuable insight into the state of current threats thanks to Infoblox’s Cyber Intelligence Unit.
The Cyber Intelligence Unit has over 10 years of experience, which allows them to create and aggregate information on threats. This allows you to take action against the discovered threats that you come across and minimizes the number of false positives that you encounter daily in the operations of your security infrastructure.
Infoblox also generates Cyber Threat Reports that are published often, providing you with useful and valuable information. These detailed reports leverage all of the knowledge, skills, and experience that are provided by their threat intelligence teams, making for readable and interesting reports.
This is an invaluable resource as it helps your team to identify current threats and vulnerabilities that other organizations are dealing with. This helps you to create and manage a cyber security plan that is relevant and up to date with regard to the current threat state around your company.
You can find these reports right over here. You can try out an assortment of different tools from Infoblox’s download section which can be found here.
A whitepaper can be found here.
Who is it recommended for?
Best for organizations requiring a holistic threat intelligence approach, with emphasis on real-time data and comprehensive monitoring of their digital ecosystem.
Pros:
- Data is pulled in from multiple sources around the world
- Easier to use than similar platforms
- Great for passive monitoring as well as manual investigation
Cons:
- The interface could use improvement
Official Website: https://www.infoblox.com
Download/Trial: https://www.infoblox.com/infoblox-download-center/
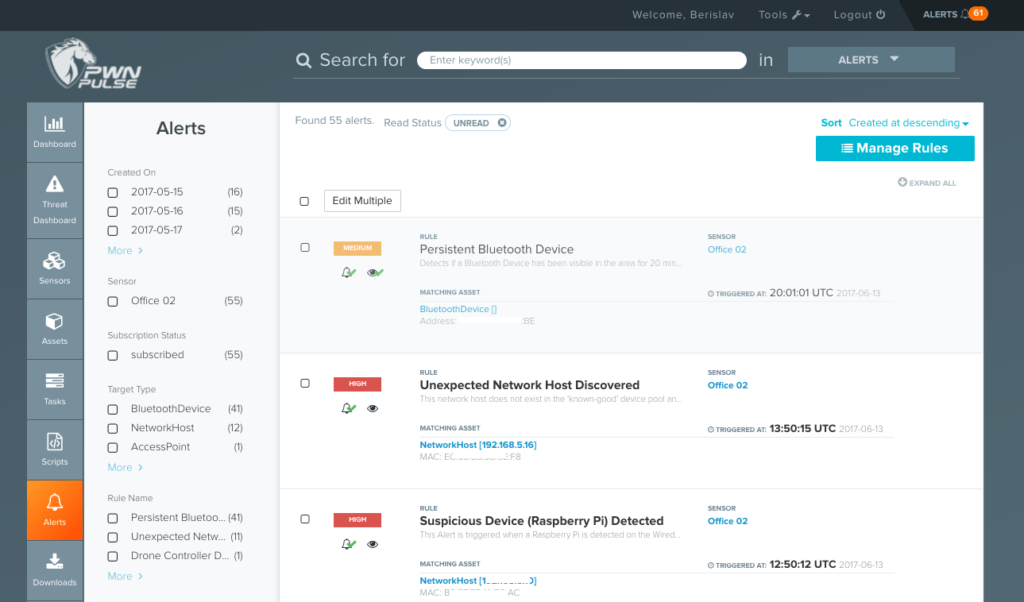
8. Heimdal Threat Hunting and Action Center
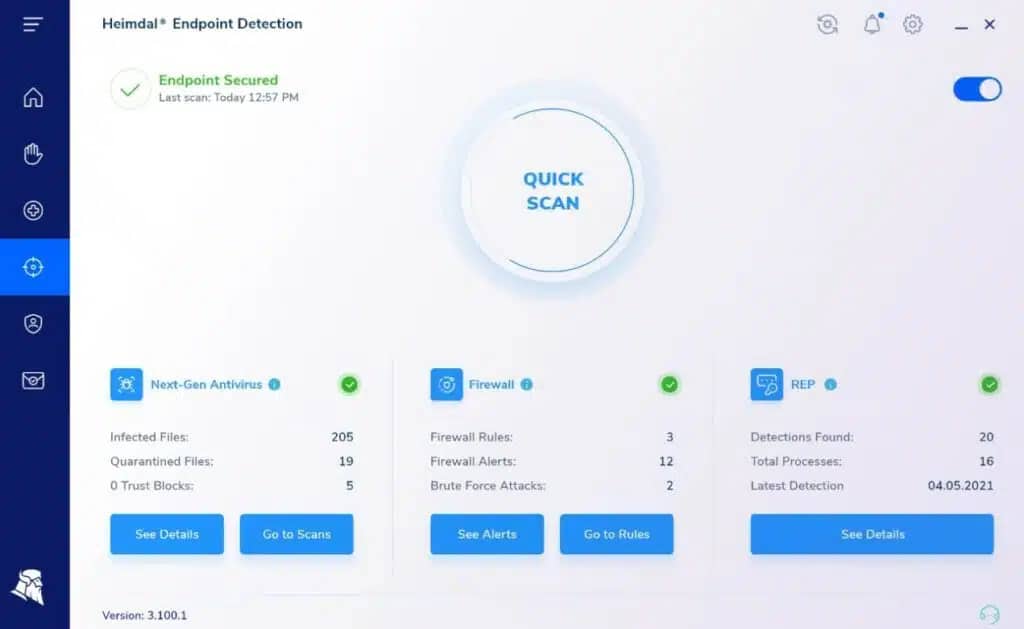
Heimdal Threat Hunting and Action Center is a cloud package that creates a threat intelligence platform for a company by working with Heimdal on-premises products. The Heimdal cloud system processes data that those on-premises units upload and it looks for threats.
The discovery of a threat triggers an automated response. That response includes instructions to the Heimdal package installed on the attacked device and also involves informing all other devices on the network.
Key Features:
- Integrates with on-premises Heimdal products
- Automated threat response
- Vulnerability manager for identifying risks
- SIEM tool for extended threat protection
Why do we recommend it?
Heimdal's Threat Hunting and Action Center offers a comprehensive cloud-based threat intelligence platform, seamlessly working with on-premises Heimdal products for an automated and effective response to identified threats.
The system includes a vulnerability manager, which identifies which on-premises devices are vulnerable to particular types of attacks. The service looks for unusual account behavior, detection evasion tactics, lateral movements, file changes, and data movements.
The platform identifies ransomware attacks and data theft attempts as well as insider threats, intruders, and malware in general. The cloud-based system relies on the client already having three different Heimdal products on the site. The Heimdal Next-Generation Anti-Virus has to be one of those three.
The NGAV installs on Windows, macOS, and Linux. It also has a mobile device management (MDM) service for Android and iOS. So, this provides details of activities on each endpoint. Naturally, it is essential to have that NGAV installed on every device.
The other two Heimdal systems that need to be on-site for the Threat Hunting and Action Center to work can be Network Security, Email Security, Patching & Asset Management, or Endpoint Security.
Having more than two of these tools in addition to the NGAV improves the performance of the Threat Hunting and Action Center system. The SIEM tool in the platform is called the XTP Engine. This is the Extended Threat Protection (XTP) system and it is linked to the automated response mechanisms in the Action Center.
This threat intelligence system is a useful system for getting an overview of all activity around a network, not just malicious activity. The Threat Hunting and Action Center looks for insider threats, malware activity, and intrusion.
The package looks for unusual user activity, detection evasion actions, file changes, data movements, communication with C&C servers, and indicators of ransomware encryption preparation.
Who is it recommended for?
Recommended for organizations already using Heimdal products, seeking a centralized system for enhanced threat intelligence and automated response capabilities.
Pros:
- Creates a threat intelligence platform for cybersecurity tools
- Warns all endpoints of a potential lateral movement threat
- Automatically blocks threats
Cons:
- No free trial
There isn’t a free trial of Heimdal Threat Hunting and Action Center but you can get a demo.
Official Website: https://heimdalsecurity.com/enterprise-security/products/threat-hunting-action-center.php
Free Trial/Demo: https://heimdalsecurity.com/request-a-demo-tac
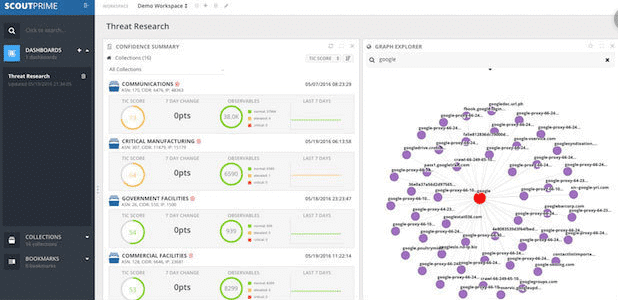
9. LookingGlass Scout Prime
LookingGlass offers a wide range of cybersecurity and threat intelligence software for modern organizations. They offer Cyber Intelligence, Managed Services, Threat Platforms, and Automated Response as part of their solutions.
Cyber Intelligence is a high-quality data suite that is customized to your organization’s specific requirements. It has data feeds that are dynamic and static, and allow for a great deal of information to be analyzed by your team.
Key Features:
- Unique footprinting capability
- Aggregates data from 88 sources
- Automated threat intelligence data ingestion
- Continuous monitoring and dynamic threat scoring
Why do we recommend it?
LookingGlass Scout Prime offers unique footprinting capabilities and aggregates data from numerous sources for dynamic threat scoring. Its continuous monitoring and automated data ingestion make it a powerful tool for proactive threat intelligence.
It has a credential monitor that also helps to detect any leaked Personally Identifiable Information for both your users and your customers. This also allows for the platform to use strategic intelligence to support whatever policies, compliance requirements and operational security considerations you might have.
On-Demand Investigations and Analysis is an augmented offering that adds value to your security team. Their Threat Platforms have two different offerings, scoutTHREAT and scoutPRIME. The scoutPRIME offering gives your team the ability to uniquely identify activities and actors by using a unique footprinting capability set that is built into the system.
It allows you to rapidly create dynamic footprints that are uniquely identifiable to any internet-accessible asset or network of interest. It essentially gives you a view from the attacker’s perspective of your organization and helps you to identify immediate risks to your company. Data relevance is critical when there is so much information being gathered about your organization.
This is why scoutPRIME is able to aggregate so many different data sources, around 88 of them in total. These data sources are threat-related and will help to generate a threat score based on what it finds. This score helps you to look at the current state of your organization, and what possible remediation steps can be taken in order to rectify the situation.
All of this is combined together to give your organization a much-needed efficiency that comes with this application. The amount of data that needs to be processed is staggering and making it meaningful is no easy task.
This is why scoutPRIME automates the threat intelligence data and ingests it so that it can be correlated and used in advanced reporting. It frees up precious cycles for your cybersecurity team so that they can concentrate on the tasks that they need to accomplish in real-time.
The system runs 24 hours a day and lets you run continuous monitoring around the clock. It monitors your vendors, networks and suppliers as well as third parties that are associated with your brand. This helps to create a wall of information that is valuable to the correlation techniques that scoutPRIME uses to gather threat intelligence for your teams.
If you wish to find out more about this platform then be sure to take a look at the datasheet that they have put together. It explains a lot of the technical details that we have outlined and gets into more detail about how everything works and fits together.
Who is it recommended for?
Ideal for organizations seeking a comprehensive threat intelligence platform with a unique approach to identifying and scoring threats, alongside automated data processing.
Pros:
- Offers cyber security as a service
- Offers SIEM services
- Can produce technical and C-level overview reporting
Cons:
- Is best for companies who want a more hands-off approach to their security
Official Website: https://www.lookingglasscyber.com
Download/Trial: https://lookingglasscyber.com/solutions/scoutprime/
10. Recorded Future
Recorded Future Express is a Threat Intelligence platform that seeks to give everybody access to some form of the technology. Recorded Future realizes that the major problem faced by most information security professionals today is not that they don’t have enough data to make informed cybersecurity decisions.
Instead, there is too much information available to threat intelligence experts. This means that it is very difficult to filter out what is important and what is noise, making the job of threat analysis that much harder.
Key Features:
- Browser extension for instant context
- Unified threat intelligence with existing cybersecurity technologies
- Enhanced alert triage and data analysis
- Access to modular widgets for dashboard customizations
Why do we recommend it?
Recorded Future stands out for its accessible browser extension, providing instant context and unifying threat intelligence with cybersecurity technologies. Its modular widgets and enhanced alert triage make it a user-friendly and efficient tool.
Recorded Future Express is a licensed product that ships with a browser extension, making it easy to instantly get context for any IP address or domain, as well as vulnerabilities and file hashes directly from inside your browser.
This is a very user-friendly approach and is sure to find favor with many professionals that find themselves with an open browser on their desktop at any given moment, day or night. This convenience makes it very quick and easy to apply the threat intelligence capabilities of Recorded Future Express at any given moment.
They have also identified the fact that too much knowledge is only one part of the threat intelligence problem. The second issue is the lack of context that is available to be used in conjunction with the information that is gathered from a threat intelligence platform.
By unifying threat intelligence with existing cyber security technologies, Recorded Future is hoping to better integrate the role of threat intelligence within a cyber security context, instead of treating it as a separate service entity.
The idea is that users that need access to threat intelligence should be able to view and work with it when they need to, without too many barriers or obstacles, especially when there are time-critical issues that need to be dealt with immediately.
This approach takes a ‘threat intelligence exclusively for all’ approach, which opens up this data source to more users than most traditional threat intelligence platforms.
This results in a few key benefits, mainly:
- Alert Triage Response Time Decreases The more eyes that are on a problem, the better. With more access to alerts you will find that more people become aware of issues much faster, reducing downtime.
- Patching Priorities A more selective approach to patching is possible thanks to enhanced threat intelligence. This saves bandwidth and time on patching, with les downtime due to system restart during updates.
- Enhanced Incident Response Indicators of Compromise combined with context provide your teams with all of the data that they need in order to deal effectively with an issue before it becomes a major issue.
- Faster Data Analysis With Recorded Future it is much faster to go through massive amounts of information. You can quickly find the most relevant parts of the reports and data and how it applies to your unique situation, and then act from there.
Additional resources such as whitepapers can be found right here.
Who is it recommended for?
Recommended for security professionals seeking an easily accessible and integrative approach to threat intelligence, with a focus on reducing information overload and enhancing data context.
Pros:
- Simple yet intuitive user interface
- Modular widgets allow for easy dashboard customizations
- Can analyze collected threat data or publically available information online
Cons:
- Must contact for pricing
- Steeper learning curve due to their use of machine learning
Official Website: https://www.recordedfuture.com/
Download/Trial: https://go.recordedfuture.com/demo
11. Webroot BrightCloud Threat Intelligence Services
BrightCloud Threat Intelligence offers is a unified service that gives developers access to a list threat intelligence services. This is accomplished through their SDKs and APIs which can be integrated into applications at a development level. This is part of the secure software design process and is a common development approach.
Key Features:
- SDKs and APIs for developer integration
- Comprehensive threat services suite
- Real-time anti-phishing and malware detection
- Mobile security SDK for mobile devices
Why do we recommend it?
Webroot BrightCloud provides a suite of threat intelligence services accessible through SDKs and APIs, making it ideal for integrating into software development. Its real-time anti-phishing, malware detection, and mobile security capabilities make it a versatile tool.
Security considerations are often included in the product design from the planning stages, and frameworks such as this help to facilitate this development philosophy. Some of the features that are available from their services are:
- Web Classification and Web Reputation This is where content classification occurs and it is run against 2 different categories, which equals billions of web pages. This helps to keep end users safe as each site has its own threat rating and can advise users not to proceed if certain parameters are met.
- IP Reputation If there are enough recorded instances of IP threats originating from a specific source then that IP will be designated with an IP Reputation, This will advise users whether or not a link s safe to proceed with, and if the IP is safe or not. This can also block malicious IPs that are known to be malicious, such as inbound malicious IP traffic.
- Real-Time Anti Phishing A purpose-built solution that helps users to quickly identify phishing activity that is suspicious. This is done before the phishing sites can open, alerting users of any abnormalities with the sites that they are trying to open.
- Streaming Malware Detection Streaming Malware Protection helps the user to stay safe by blocking malicious traffic as it is streaming via the user’s connection. If files are deemed to be unsafe, or from an unknown or untrustworthy source, then that traffics is blocked by the service.
- File Reputation If there have been malicious reports associated with specific files that have a name or size and signature that matches, then users will either be warned not to execute such files, or they will be blocked from downloading them all together.
- Mobile Security SDK So many users access the internet via their smartphones primarily, which has meant that mobile security has had to catch up with the ever-evolving cyber threats that are aimed specifically at mobile devices. The UI-less SDK can be embedded directly into mobile solutions and help to prevent malicious activity from affecting users.
The solution also offers Supplementary Intelligence in the form of contextual Database APIs and Threat Insight APIs, which are incredibly useful for software developers.
Who is it recommended for?
Best suited for developers and organizations looking to integrate advanced threat intelligence services directly into their software or mobile applications.
Pros:
- Takes a unique approach to ransomware detection with “bait” files
- Can defend against both known and unknown forms of ransomware attacks
- Offers protected folders that prevent ransomware from accessing them
Cons:
- Enterprise networks may require more control and features in their anti-ransomware tool
Official Website: https://www.webroot.com/us/en/business/threat-intelligence
Download/Trial: https://www.webroot.com/us/en/business/about/contact-us/brightcloud-contact-us
Conclusion
There are many different Threat Intelligence Platforms available today, mainly due to the vast amount of continually evolving threats that surface daily on the internet. As each threat becomes more sophisticated and difficult to detect, the countermeasures that you implement will have to keep up.
Depending on your budget and requirements there is something for everyone on our list. We hope that you have found this useful and that you can make better decisions after looking at each of these products’ core features.
Threat Intelligence Platforms FAQs
What types of threat intelligence data can be collected by a platform?
Threat intelligence data can include information about known vulnerabilities, malware, phishing campaigns, IP addresses, domains, and other indicators of compromise.
What are the benefits of using a threat intelligence platform?
Using a threat intelligence platform can help organizations improve their security posture by providing real-time threat intelligence data, enabling faster incident response times, and allowing for proactive threat hunting and mitigation.
How does a threat intelligence platform collect and analyze data?
A threat intelligence platform may collect data from a variety of sources including open source intelligence (OSINT), proprietary sources, and internal sources. The data is then analyzed using machine learning and other analytics tools to identify patterns and potential threats.
What are some common features of a threat intelligence platform?
Common features of a threat intelligence platform include threat detection and analysis, automated response and remediation, customizable alerts and reporting, and integration with other security tools and systems.
What types of organizations can benefit from using a threat intelligence platform?
Any organization that has a need to identify and mitigate security threats can benefit from using a threat intelligence platform, including enterprises, government agencies, and small and medium-sized businesses.
What are some common threat intelligence platforms?
Common threat intelligence platforms include Datadog Security Monitoring, ThreatQuotient, Recorded Future, FireEye iSIGHT, and Anomali.
How can I select the right threat intelligence platform for my organization?
To select the right threat intelligence platform for your organization, consider factors such as the types of threats you are most concerned about, the features and capabilities that are most important to your organization, and the cost and licensing model of the platform.
Can threat intelligence platforms be integrated with other security tools?
Yes, many threat intelligence platforms can be integrated with other security tools such as SIEMs, firewalls, and endpoint protection tools. Integration can help organizations automate threat detection and response and streamline their security operations.