Are you wondering what virtual patching is and its importance in vulnerability management? If yes, you have landed at the right place. We will have a look at the introduction of virtual patching, the value of virtual patching, what makes patching difficult for businesses, and how to fix the virtual patching issues. So without any delay, let's get started.
What is Virtual Patching?
Virtual patching is the process of developing and deploying a temporary strategy to limit the risks of exploitation connected with the discovery of new security vulnerabilities. It eliminates the possibility of hackers identifying and exploiting application or system security flaws.
The main goal of virtual patching is to prevent malicious traffic from accessing a vulnerable application while still implementing the security fix. It enables developers and security administrators to keep an application/system operational until a vulnerability remedy is discovered, developed, and tested. The patch is installed on a small number of hosts/systems and can be replicated/covered across the application environment. However, virtual patching is not a long-term solution and does not always detect all software/system vulnerabilities.
Value of Virtual Patching
Virtual patching, also known as vulnerability shielding, protects against threats that exploit known and new vulnerabilities. Virtual patching works by enforcing layers of security policies and regulations that prevent and intercept exploits from following network paths to and from exposures.
A multilayered virtual patching approach is ideal. This includes features for inspecting and blocking harmful activities in business-critical traffic, detecting and preventing intrusions, thwarting assaults on web-facing apps, and deploying with adaptability on physical, virtual, or cloud platforms.
Here's how virtual patching complements an organization's existing security technology and vulnerability and patch management policies:
- It buys you more time Virtual patching allows security teams to assess the vulnerability, test, and install the necessary and permanent patches. In-house applications benefit from virtual patching since it gives developers and programmers more time to resolve vulnerabilities in their code.
- Prevents unnecessary downtime Virtual patching gives organizations more flexibility in enforcing patch management practices on their timetable. This reduces the possibility of income loss due to unplanned or unnecessary disruptions in corporate activities.
- Enhances regulatory compliance Virtual patching assists firms in meeting timeliness requirements like those required by the EU General Data Protection Regulation (GDPR) and the Payment Card Industry Data Security Standard (PCI DSS) (PCI).
- It adds an extra layer of security Virtual patching extends security controls to IT infrastructures for which updates are no longer released (e.g., outdated systems and end-of-support operating systems such as Windows Server 2008) is prohibitively expensive to patch.
- Allows for greater adaptability Virtual patching eliminates the need to distribute workarounds or emergency patches. It facilitates tasks such as determining specific places in the network that require patching (or if a patch requires to be applied to all systems).
When you examine the numerous instances in which businesses cannot simply modify the source code quickly, the usefulness of virtual patching becomes clear. Regarding the organization, the benefits are as follows:
- It enables businesses to keep typical patching cycles.
- It lowers risk until a vendor-supplied patch is released or while a patch is tested and applied.
- It is a scalable approach because it is done on a few sites rather than on all hosts.
- Because libraries and support code files are not modified, there is less chance of introducing conflicts.
- It protects mission-critical systems that cannot be taken offline.
- It cuts or eliminates the time and money spent on emergency patching.
From the standpoint of a web application security consultant, virtual patching opens up another channel for providing services to your clients. Historically, if source code could not be changed for any of the reasons listed above, there wasn't much else a consultant could do to assist. A consultant can now offer to generate virtual patches to solve issues outside of the application code.
What makes patching difficult for businesses?
Some of the difficulties that businesses experience while implementing a vulnerability and patch management policy are as follows:
- Continuity of operations While applying updates regularly is a desirable practice, many businesses find the patching process so long, disruptive, and expensive that they choose to postpone it (or do away with it entirely) to minimize operational disruption.
- The number of vulnerabilities that must be patched This is especially true for firms that must patch a growing number of vulnerabilities as their IT infrastructures are regularly upgraded. Our statistics, which includes contributions from over 3,500 independent researchers who participate in our Zero Day Initiative (ZDI) program, identified and reported vulnerabilities grew by 40% between 2019 and 2020.
- Visibility is limited More extensive internet infrastructures necessitate more complicated update procedures. This could be exacerbated by a fragmented IT infrastructure, which is typically made up of several operating systems or application versions that are sometimes also geographically scattered.
- Patch cycle frequency This can make patching challenging to control adequately, especially when determining which vulnerabilities are the most significant or urgent.
- Systems that are no longer patchable Patches may no longer be delivered to systems and applications that have reached the end of their life cycle or support, even if they are still needed to perform mission-critical tasks. Embedded systems, such as POS terminals, IoT devices, and industrial control systems, frequently contain software or components that cannot be patched.
What happens to IT infrastructures that aren't patched?
When a vulnerability is revealed, reported, or discovered, companies are in a race against time. It's a golden chance for cybercriminals and threat actors. A typical firm, for example, is said to take 69 days to fix a critical vulnerability in its application. Businesses in the United Kingdom took an average of 60 days to realize they had been breached.
This window of vulnerability exposes unpatched systems to attacks. Threat actors began ransomware attacks against unpatched servers in January 2020, putting the networks of over 80,000 businesses at risk.
From a purely technical standpoint, the most effective remediation technique would be for a business to fix the identified vulnerability within the web application's source code. Both web application security specialists and system administrators agree on this approach. Unfortunately, there are numerous cases in real-world business situations where upgrading the source code of a web application is complex. The following are some of the most common impediments to source code fixes:
Availability of patch
If a vulnerability is discovered in a commercial program, the customer is unlikely to edit the source code. The consumer is at the vendor's mercy in this case because they must wait for an official fix to be provided. Because vendors typically have fairly strict patch release time frames, an officially supported patch may not be accessible for a prolonged time.
Time of Installation
Even when an official patch is available, or a source code repair can be deployed to a custom-coded program, most businesses' usual patching processes are time intensive. This is typically due to the considerable regression testing that is required following code modifications. It is not uncommon for these testing gates to take months to complete.
The Symantec Internet Threat Report, for example, stated that the average time it took organizations to patch their systems was 55 days, In contrast, the WhiteHat Security Web Security Statistics Report indicated that their customers' time-to-fix average was 138 days to remediate SQL Injection vulnerabilities discovered in their web applications. When this patching data is contrasted with Symantec's revelation that it only took an average of 6 days for exploit code to be exposed to the public, it is evident that standard source code patching techniques are insufficient.
Fixing Custom Code Could Be Expensive
Web assessments that involve source code inspections, vulnerability scans, and penetration testing tools will almost certainly uncover flaws in your web application. Identifying of the vulnerability is merely the first half of the battle; the repair activities are the second half. Many firms are discovering that the expense of identifying vulnerabilities often pales in contrast to the cost of actually correcting the concerns.
This is especially true when vulnerabilities are discovered after a program has already been deployed rather than during the design or testing phases. In these cases, it is frequently determined that recoding the application would be prohibitively expensive.
Legacy Code
An organization may be utilizing a commercial application whose vendor has gone out of business, or they may be using a version that the seller no longer supports. Legacy application code cannot be patched in these cases. Another scenario is when an organization is obliged to use obsolete vendor code due to in-house custom-developed functionality built on top of the original vendor code. This feature is linked to a mission-critical business program, and previous upgrade efforts ruined it.
Outsourced Coding
As more firms choose to outsource their application development, they discover that implementing vulnerability patches necessitates creating an entirely new project. Many firms are confronted with the sad fact that inadequate contractual wording frequently does not cover “secure coding” issues but just functional flaws.
How to fix Virtual Patching issues?
Software patching is both a solution for code flaws and a source of dissatisfaction because it adds to the network administrator's burden. So, what is the significance of precise and timely patching of susceptible systems?
Patching a vulnerable system might take days, weeks, or even months, especially if there is an issue that patching may interfere with the app's basic functionality.
There are a few obstacles that make patching even more complicated:
Cost reduction — The IT team may postpone software patching because it may necessitate an expensive upgrade or replacement of the legacy system or the rebuilding of an enterprise application.
Official Patch Deployment – Patching may be delayed if the software vendor does not make it available.
Uptime Preservation — The IT team may stop patching because it may need to take the business-critical servers offline.
Cybercriminals are constantly racing to exploit newly identified vulnerabilities before organizations have a chance to defend themselves. According to FireEye Mandiant Threat Intelligence Research, most vulnerability exploitation occurs before the patch's delivery or within a few days after the patch's issuance.
The rapidity with which hackers exploit vulnerabilities emphasizes the importance of updating as soon as feasible. However, a delay in patching puts the organization at risk of attack, and cybercriminals gain all of the information they need to exploit, resulting in the following issues:
Compromise in security measures.
- Exposed Critical Data
- Compromise between the network and the system.
- Loss of Reputation.
- Financial setback.
With an increasing number of security vulnerabilities published each year, it can be difficult for organizations with business limitations and limited resources to apply updates as soon as possible. Deep security virtual patching, for example, can help with patch management by covering both known and unknown vulnerabilities.
Indusface AppTrana
One solution to the overwhelming task list that operating Web assets creates is to select a managed service to handle all of those jobs. Indusface AppTrana is a WAF platform and it is offered with technicians to provide security operations for your Web systems. This is the Premium package of AppTrana and it adds on vulnerability scanning, virtual patching, and penetration testing services to the WAF cloud platform.
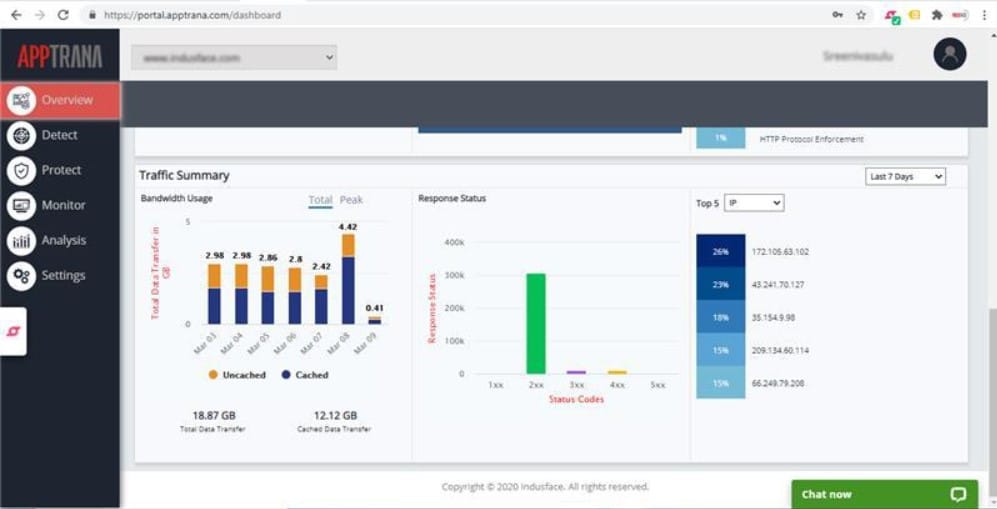
You can get a look at the tools offered in this package by accessing a 14-day free trial of the unmanaged Advance edition of AppTrana.
Conclusion
Keeping up with security issues in complex web apps and software in today's ever-changing environment can be exhausting. In these situations, virtual patching comes in handy. It mitigates risk by patching web app vulnerabilities.
Virtual patches have various advantages over regular patching cycles, consuming a significant amount of time, effort, and money. Virtual patches can be installed in minutes or hours at a low cost. Furthermore, they should be incorporated in the security toolbox with other security technologies such as firewalls, intrusion prevention systems, and better defense against developing threat and attack strategies.
Virtual Patching FAQs
How does virtual patching work?
Virtual patching works by deploying a security policy or rule to a system or network to block or limit access to a vulnerable system or application. This policy or rule is designed to address the specific vulnerability without requiring a traditional software patch.
What are the benefits of virtual patching?
The benefits of virtual patching include the ability to protect against known vulnerabilities before a patch is available, the ability to reduce the risk of a security breach, and the ability to minimize the impact of a security incident.
What types of vulnerabilities can be addressed with virtual patching?
Virtual patching can be used to address a variety of vulnerabilities, including those in operating systems, web applications, and databases.
What are some common virtual patching solutions?
Common virtual patching solutions include network-based intrusion prevention systems (IPS), web application firewalls (WAF), and database firewalls.
How can virtual patching be integrated with other security solutions?
Virtual patching can be integrated with other security solutions such as vulnerability scanners and threat intelligence platforms to provide a comprehensive security strategy.
How do I know if virtual patching is right for my organization?
Virtual patching may be right for your organization if you need to protect against known vulnerabilities before a patch is available or if you need to minimize the impact of a security incident.
What are some best practices for virtual patching?
Best practices for virtual patching include regularly updating security policies and rules, testing virtual patches in a lab environment before deployment, and monitoring for false positives and false negatives.
What are some limitations of virtual patching?
Limitations of virtual patching include the need for regular updates to security policies and rules, the potential for false positives and false negatives, and the fact that virtual patching does not address the underlying vulnerability.
Can virtual patching replace traditional patching?
No, virtual patching cannot replace traditional patching, as it does not address the underlying vulnerability. However, virtual patching can be a useful supplement to traditional patching, allowing organizations to protect against known vulnerabilities while waiting for a patch to be released.